With the increase in the number of remote workers, cybersecurity is becoming more and more important. While there are many crucial factors in effective corporate security measures, email security is one of the first areas that should be addressed.
Targeted email attacks are on the rise
Virus and malware infections via email remain the most damaging type of cyber-attack and are continuously evolving. In particular, targeted email attacks are increasing, designed for and aimed at specific individuals and companies.
Targeted email attacks are sophisticated methods to trick employees to click on malware links or attachments sent under the guise of a business partner or customer. Because these emails look just like normal business emails, it is possible that malware can be unknowingly downloaded.
Emotet: a new malware threat
Recently, a new malware similar to targeted email attacks, Emotet, has been on a global rampage since 2019. Like targeted email attacks, the Emotet infection starts when a link or attachment in cleverly crafted spam emails is clicked.
The scary thing about Emotet is that, once activated, it multiplies by attacking the company's network and spreads rapidly.
“Don’t read” and “Don’t open” are no longer enough to maintain email security
One reason behind the spread of Emotet's infection is the speed of its evolution. Every time a file is registered in an antivirus software database, it evolves by changing its file format and other features to become undetectable, creating a dangerous game of cat-and-mouse.
It has also become clear that the techniques for tricking email recipients are becoming more and more sophisticated. These days, many of these emails cannot be identified as spam without a great deal of caution, and the risk of infection cannot be mitigated by vigilance and basic anti-virus software on the recipient's side alone.
Block dangerous emails with Tsukaeru MailBuster!
Tsukaeru MailBuster is the latest solution for dealing with increasingly sophisticated and evolving email attacks. Tsukaeru MailBuster has the following features:
・Completely cloud-based: no need for software installation or updates on individual computers
・Virus blocking rate of 100% and spam blocking rate of 99.98%
・Supports ransomware countermeasures and Office 365
・Unique filtering system, which utilizes learning AI technology, shutting out even unknown threats
・No initial investment required (1,600 yen monthly cost/100 email accounts per domain)
Visit the Tsukaeru website to learn more!
Tsukaeru MailBuster – click for details
Contact us at Tsukaeru.
In June, the restriction on crossing prefectural borders was lifted in Japan, and in Europe, there is a movement to gradually open borders. It seems that the world is slowly moving to the normality of the past.
However, after this unprecedented crisis, there is one thing that is unlikely to be completely restored even if the pandemic disappears: our way of working.
Three keywords for defining work in the post-Corona age
With the spread of the Novel Coronavirus, many companies experienced remote work for the first time. Now, it seems that more and more people will return to regular work in the near future, but even so, many managers believe that everything cannot be restored to what it once was.
In the post-Corona age, where productivity and work-life balance are more important than ever, the three keywords are “collaboration,” “flexibility,” and “security.”
■ Collaboration
Accelerating innovation through collaboration with other companies and the use of freelancers will become more and more common in the future. Collaboration with outside entities is an efficient way to create new value and profit in the shortest time possible.
■ Flexibility
From this experience, many will realize that remote work is in fact possible. From now on, not only large companies, but also small- and medium-sized ones, will accept more flexible work styles to some extent, according to employee circumstances and lifestyles.
■ Security
Strengthening information security is essential to promote the collaboration and flexibility mentioned above. Instead of a passive attitude of “implementing minimum measures,” a positive mindset of “always pursuing the best and latest security measures” is required.
Will cloud storage become commonplace in the post-Corona age?
In order to strengthen collaboration with others and promote more flexible working styles, it is important to create an environment that enables smooth and secure file exchange. However, project management and file version management can quickly become complicated with the use of conventional email attachments.
To meet this need, the use of cloud storage is rapidly expanding. Files can be easily uploaded and downloaded when needed and are always updated to the latest version. There is no need to keep track of which version was sent to who when. Another advantage is that it does not require labor or cost to operate the file server in-house.
Reasons to use Tsukaeru Filebako
Tsukaeru’s Filebako cloud storage service is used by many companies, organizations, and educational institutions nationwide. Here are some excellent reasons for this growing support:
■ Easy and smooth collaboration
Packed with functions that facilitate collaboration, such as shared folders that are ideal for teamwork inside and outside the company, and weblink sharing that allows hassle-free file sharing. The simple and attractive interface facilitates immediate use.
■ Fast flexibility and work style diversity introduction
Tsukaeru Filebako is perfect for remote work file exchange. The official app (iOS and Android) allows remote work anytime and anywhere.
■ Highest-level security and full support
In addition to SSL communication, double encryption with a secret key is provided. Access authority for each file/folder and device/login history confirmation is readily available. Customer support from highly-experienced in-house staff is always available to help.
To be better prepared for the post-Corona age, why not consider trying Tsukaeru Filebako? To learn more, especially about our exciting 14-day free trial membership, please contact us!
Tsukaeru Filebako service details
Please visit the Tsukaeru website to contact us for more information.
Servers are essential for running a company’s websites or systems.
While it is common to choose a “dedicated” or “shared” server, do you know about the new, popular “VPS” option?
What is VPS in the first place?
VPS stands for “Virtual Private Server,” and as the name implies, the basic idea is to create a dedicated server in a virtual environment.
What makes VPS a game-changer is that one physical server is virtually divided by “virtualization technology” for each user. By adopting this technology, it is possible to create multiple “virtual servers” in one physical server and place independent environments (individual memory, disk space, software, etc.) each one.
Since each virtual server is independent, there is little chance that one will affect another.
DIfferences between VPS, dedicated servers, and shared servers
A dedicated server is a service in which one physical server is contracted for the exclusive use of the customer’s choice. It provides the highest degree of flexibility and stability but a slightly higher cost.
A shared server is a service where multiple users share a physical server. It has the lowest price and is a popular choice with those who just want simple usage (site operation, mail account management, etc.) One disadvantage can be limited custom settings and usage may be affected by other users.
VPS is a service that balances the benefits of both, providing a similar flexibility to that of a dedicated server along with lower costs like a shared server.
What is the difference between a container type VPS and VM type VPS?
There are two main types of VPS: container type and VM type.
The container type is a method of realizing virtualization by arranging a package called a “container” (a collection of software and various operating environments ) on one host operating system.
The VM type, on the other hand, is a method for realizing virtualization by preparing a guest operating system for each user on top of the host operating system and creating a “virtual machine” like a dedicated server.
The container type VPS has the following advantages:
・Effortless operation
・Flexible and effective use of resources
・Simple and easy environment construction
The VM type VPS has the following advantages:
・User can select guest operating system
・More finely customizable than container type
Recently, users are more likely to select the flexible container type, but in some cases, VM type is the better option if more detailed settings are necessary.
Advantages of Tsukaeru Cloud VPS
Tsukaeru Cloud VPS is becoming a popular VPS service of choice. Here is a summary of some of the advantages:
・Flexibility::Container or VM type can be selected. For VM type, Linux and Windows operating systems can be chosen.
・High availability(HA configuration):In the unlikely event of a physical failure, relocation of services will take minutes as compared to several hours.
・Plesk:Equipped with Plesk, the latest version of the powerful and easy-to-use server management tool, you can easily manage your server from the browser window.
・Various templates: Server specifications can be selected to create combinations to suit your needs.
・Safe and secure: Tsukaeru servers operate in an extremely secure domestic data center with the highest levels of
security always maintained.
50% Off Tsukaeru Cloud VPS Campaign!
Currently, Tsukaeru Cloud VPS is being offered at a 50% discount. In addition, if you sign up for a one-year contract, the initial setup costs will be waived. This campaign is only available until June 30th, 2020, so don’t miss the chance!
Learn more about Tsukaeru Cloud VPS here.
Contact Tsukaeru here.
An increasing number of people are becoming marketing affiliates as a way to earn extra money on the side. However, while many may have heard of the term, they may not know how it works or think that it is difficult to get started. In this month’s article, we will introduce the basics of affiliate marketing and what you need to know.
What is affiliate marketing?
Affiliate marketing is a way to earn money by placing advertisements on your blog or website. Basically, the reward comes from the following flow:
1. Register with an intermediary company called an Affiliate Service Provider (ASP)
2. Select the product/service you want to introduce from the ASP site
3. Introduce the product/service with banner ads on your blog or website
4. If a user reads an introductory article, clicks on an advertisement, and purchases a product or contracts a service, a reward is generated accordingly
As rewards increase according to the number of achievements (product purchases and service contracts), it is important to identify and post better products and services, and to clearly introduce their merits.
Benefits of becoming an affiliate
Why are so many people getting into affiliate marketing now? Reexamining the following benefits may explain why:
・No initial investment is required
・With access to the internet, you can easily start with basic skills or knowledge
・One product introduction can lead to many views
Because affiliate marketing has almost zero risk and a low threshold to start, it is recommended for beginners who have little experience with this type of side job. If you already have a blog, it will take little effort to quickly get up and running.
What’s different about Tsukaeru’s Affiliate program?
Did you know that Tsukaeru has its own affiliate program that you can actually use? Our affiliate program is packed with benefits that are a bit different from others.
1. Easy application without an ASP! OK to just share a promo code
Tsukaeru affiliates do not need to paste banner advertisements. Also, the application is easy since there is no need to use any ASPs for intermediary purposes. You can just apply from our official website.
After registering for our affiliate program, a unique token (promo code) is issued. To introduce it to a wider audience, you can just share the token, not only on your blog or website, but also on any platform such as SNS, email, and chat. It is also possible to put the token on business cards and posters.
The token can be customized as per your preference (you need another application). You can have your favorite name which is easy to remember!
2. Two rewards systems to choose from
There are two types of reward options: “Batch Reward,” which is ideal for those who want to receive awards immediately, and “Continuous Reward,” which is optimal for those who want to receive rewards continuously. For the first type of reward, you would receive a fixed reward for each contract completed (i.e. Tsukaeru Cloud VPS 8GB → 6,000 JPY). For the second type, you would receive a monthly “usage fee x 10%” per contracted customer until the contract is cancelled (i.e. Tsukaeru Cloud VPS 8GB → 1,200 JPY/month).
3. Reliability due to popular, high quality service
Because Tsukaeru has 20 years of experience and many users both in Japan and overseas, you can recommend it with confidence.
At the end of the year and during the holidays, many people surf the web, increasing the number of visitors to blogs and websites. This is a perfect time to become an affiliate. Why not take advantage of this traffic and aim for an easy supplemental income with Tsukaeru’s Affiliate program?
Click here for details about Tsukaeru’s Affiliate program
Click here to sign up for Tsukaeru’s Affiliate program
Although email is still indispensable for businesses as a means of communication, there are always problems with spam emails. They not only interfere with efficient operations, but also pose serious security risks due to viruses or phishing attacks. To better understand, let’s take a look at the actual status of spam mail.
Approximately 40% of emails received in Japan are spam
In looking at the numbers, the overwhelming amount of spam email is the first thing that stands out. According to statistics from the Ministry of Internal Affairs and Communications, approximately 750,000,000 spam emails are received in Japan every day (as of March 2019) – about 44% of all emails! In recent years, this ratio of spam emails to all emails has consistently been between just below 40% and around 50%, with no major improvement observed.
In looking at the countries and regions that are the sources of spam emails received in Japan, the top five as of March 2019 are Japan (35.85%), the United States (9.02%), Brazil (6.52%), Hong Kong (5.63%), and Russia (5.62%). It is obvious that Japanese users and companies are targeted by attackers from around the world.
Rapidly increasing threat of Business Email Compromise (BEC)
Spam email contents are usually related to dating services, information products, and finance. Recently, a type of email fraud called business email compromise (BEC) has been rapidly increasing. BEC is an email scam that attempts to gather data or gain access to financial accounts by pretending to be from a company executive or a trusted customer. Total BEC losses in the United States in 2018 reached around $1.2 billion. The number of BEC attacks in 2014 was about 200, but in 2018, it exceeded 20,000 (based on FBI data).
Japan is also experiencing an increase in targeted email attacks that attempt to obtain information. According to statistics from the National Police Agency, there were 1,723 targeted email attacks in 2014, and that number has rapidly increased to 6,740 in 2018*.
What is the key to preventing spam?
The key to keeping your company safe from spam email is “block before receiving.” It is common to use an email software’s filtering function as a countermeasure against spam emails. However, it is not perfect. This filtering function is based on receiving all emails and then sorting out the spam, which can tie up valuable server capacity and bandwidth. There is also a concern that viruses and malicious software attached to spam emails may enter your network.
Easily block junk mail with “Tsukaeru MailBuster”
We would like to recommend our “Tsukaeru MailBuster,” a complete cloud-based service for your email. Tsukaeru MailBuster can be used to block junk email, spam emails, emails with viruses, etc. before they reach your email server. Our unique filtering system uses learning-type AI technology to achieve 100% accuracy against viruses and 99.98% accuracy when dealing with spam. It is extremely effective as a countermeasure against ransomware and targeted email attacks.
As Tsukaeru MailBuster is cloud based, no initial investment is required, and it is easy to implement and start for as little as $15 per month. With our continuously improving accuracy and response to new malware and other threats based our own self-learning smart technology, you don’t have to worry about troublesome updates. If you have trouble with spam email, please check out our excellent MailBuster service.
Click here to learn more about Tsukaeru MailBuster
Click here to contact Tsukaeru
*Reference and data source: 2019 White Paper on Spam Email – Spam Countermeasure Promotion Council (PDF)
When creating the design for a website or application, developers tend to overlook one crucial aspect: usability. Usability encompasses the entire user experience and it directly influences the success you receive with your customers. Are you convincing visitors to do business with you? Are you persuading them to come back? How satisfied are they with the overall experience? Is that more or less satisfied than their experience with your competitors? Usability determines the answers to these questions.
Despite being so important, the user experience tends to get neglected, especially since its effects cannot be measured in numbers. To ensure you're creating the highest possible level of usability, let's examine the topic further:
Understanding Usability
What exactly is meant by ‘the user experience’ or ‘usability’? In a nutshell, it's the ease-of-use of an application or website. In other words, it's the degree to which a user can achieve the purpose of a product with efficiency and without stress. The success of a product or service is based on this essential aspect.
When usability is poor, users are not able to achieve their goals properly and efficiently – this leads to frustration. Users quickly get tired of low usability and this will result in them quitting the experience entirely. Don’t forget that the internet is full of alternatives to any product or service. At its worst, poor usability can lead to a disastrous loss of customers.
Factors that Affect Usability
There are many complex elements that affect the overall user experience, but the most important factors are:
Websites and applications need to achieve their goals without any errors arising. To achieve this, certain design specifications should be implemented with the user's point of view in mind. For example, consider a payment page where the field for entering a credit card number has no restrictions on the number or type of characters entered. This means it would be possible for a user to enter a name or address instead of a number. When the error page is received, the user's frustration will begin to build. Visitors have a low tolerance for trial-and-error.
To improve the usability of this particular experience, designers and developers should ensure there is a specification in place that only allows numbers in certain fields and with a character limit. This may seem like a minor feature, but it can greatly influence the overall experience your site creates.
Efficiency is not just about how possible it is for users to achieve their goals, but also, how fast. How many steps must users take before they get what they need? Are there difficult-to-understand buttons or fields which will slow them down? A good rule for improving usability is to consider what the most important goal is and reducing the number of steps or time it takes to achieve that goal.
To increase a website or application’s level of engagement, there needs to be clarity. Make your message simple and get straight to the point. Copious amounts of copywriting, irrelevant information, or badly structured layouts will cause your visitors to disengage. Has the necessary navigation been implemented? Is the text clear? Are your visitors aware of what they need to click on? Is your layout cluttered and distracting? Or is it plain and unattractive?'
Having aesthetically pleasing designs can raise levels of engagement significantly, but it won’t do the trick on its own. Focus on easy-to-navigate layouts, intuitive positioning and design, and clear, inviting copywriting. This step to usability is important because, without it, you can lose visitors even if your product is excellent. To ensure that you are receiving a high amount of traffic, add clarity to all aspects of your service and product. Make the experience straightforward and clean, instead of stressful and confusing.
You may have a top-notch website with engaging content like https://facetimeforpc.site, but if users cannot access it when they need it, this defeats the entire purpose. The availability of an application or website is a core aspect of usability. This will create frustration for users and you’ll lose them in an instant.
To improve the accessibility of your service, consider investing in quality hosting, such as Tsukaeru’s web hosting. The amount of server uptime you receive will directly affect the usability of your website and the number of customers that reach you. For the best results, decrease or eliminate the possibility of errors arising. In addition to this, update links on your service regularly. Make sure there are no broken links that lead users to dead-ends. Not only is this frustrating for the user, but it gives the impression that your service is out-of-date.
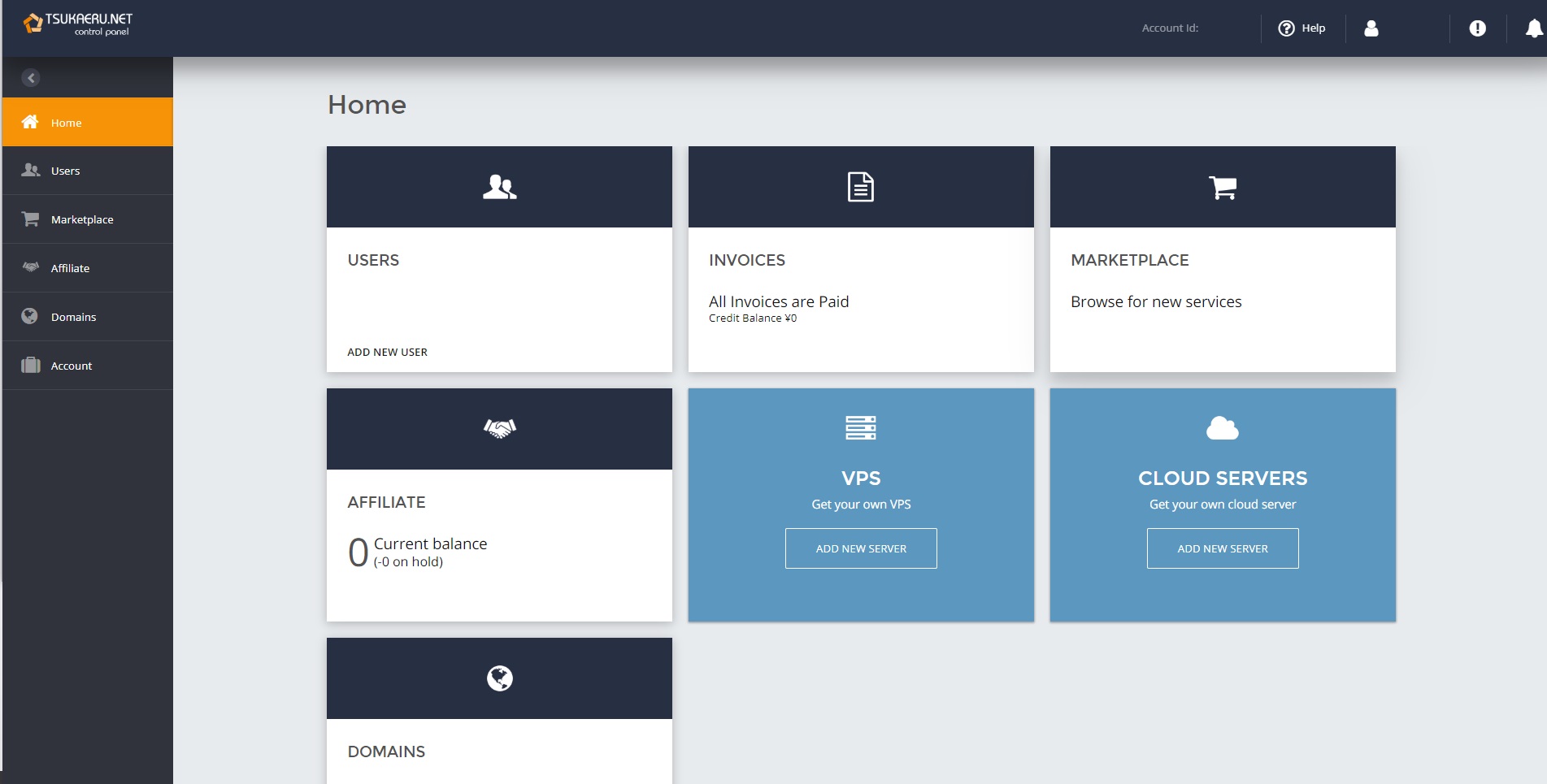
Increased Usability with the New Tsukaeru Control Panel
At Tsukaeru, great care is taken to ensure we provide users with an easy, satisfying, and stress-free experience. For this reason, we’ve enhanced the usability and revamped the design of our control panel. On this new and improved page, Tsukaeru.net members can enjoy a more intuitive UI design that allows one to easily keep track of their services, payment status, or add new services, such as the Tsukaeru Cloud Backup.
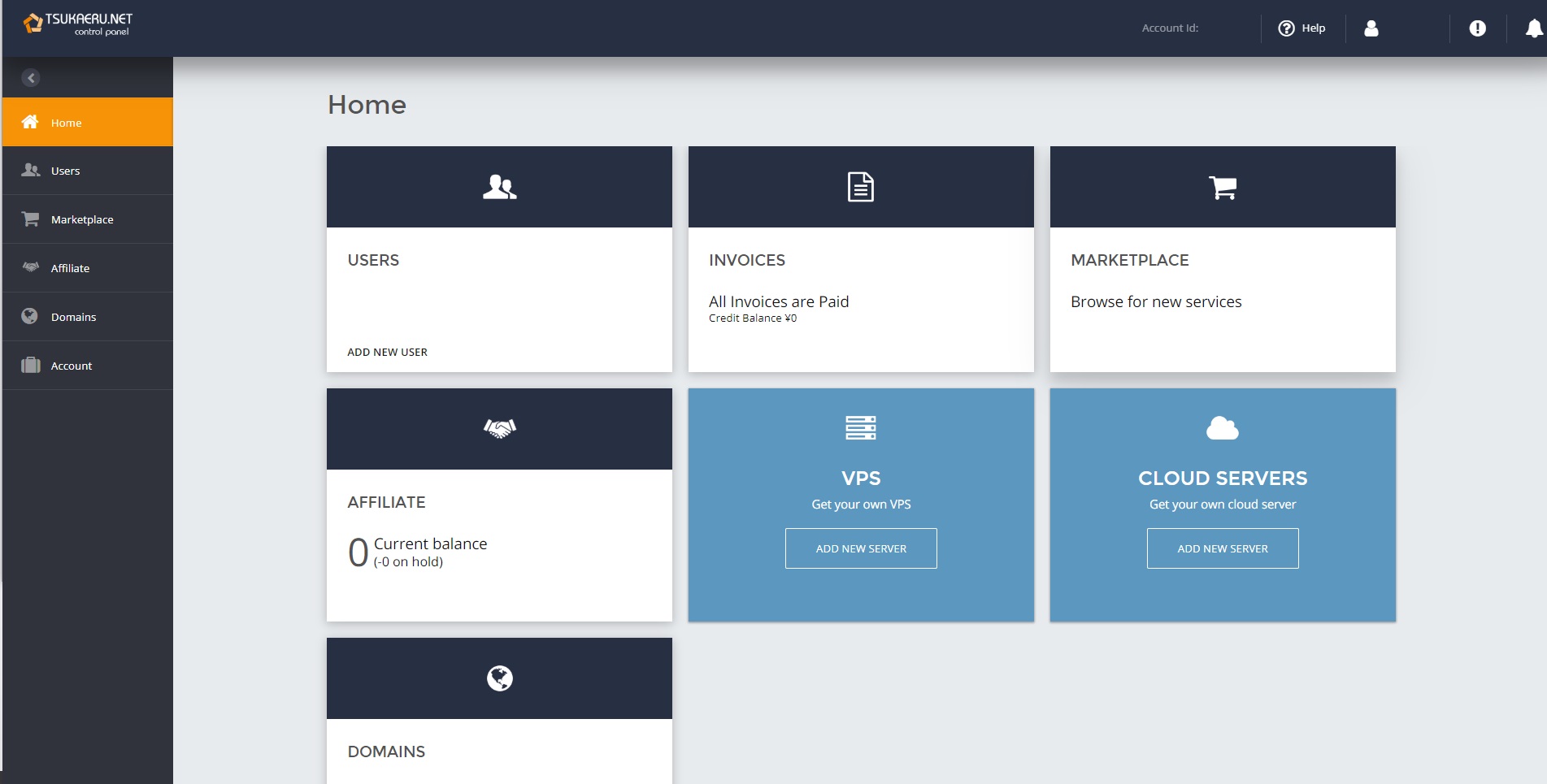
These changes will be visible to everyone with a new Tsukaeru account, but all users are welcome to receive this update if they so choose. Please feel free to contact us if you have an existing account that you’d like to update.
Contact Us
Natural disasters, fires, system failure, cyber-attacks: these are some of the many brutal risks a company can encounter. How well we respond and how we continue business activities after these unforeseen situations will determine the company’s strength and fate. This is particularly true in Japan, where powerful earthquakes are known to occur. There’s no telling when one might strike. Why not take this opportunity to consider your Business Continuity Plan (BCP) in the event of a disaster?
Companies and BCPs Today
A recent survey conducted has shown only a shocking 15% of companies have developed a BCP. According to this statistical survey, responses that a BCP had been developed, was in the process of being developed or development was being considered totaled to a surprisingly low 45.5%.
The most frequently cited reason for not developing a BCP is not having the necessary skills and not knowing how to go about formulation. Though many companies recognize the need for a BCP, it appears as if most aren’t sure exactly what formulation entails.
So what measures are necessary for business disaster prevention? What can businesses include in their plan for business continuity? Here are some examples:
- Develop communication systems for times of disaster.
- Identify alternative contact tools and services to the ones used daily, to prepare for the event they are not available during a disaster.
- Establish data backup and recovery methods.
- Shared use of cloud services.
- Establish a disaster prevention manual.
- Implement disaster prevention training.
- Redundancy of servers and internal systems.
Tips for Improving Your Disaster Recovery Plan
A BCP and disaster recovery plan are pointless if they’re not practical. Here are some tips for creating a successful recovery plan:
Determine the appropriate response for different levels of disaster
Is it a big earthquake that causes massive damage? Or is it system or power failure that strikes unexpectedly? The correct response to these occurrences will vary depending on the scale of damage and the type of disaster. It’s important to consider these different types and levels of disasters, and identify the response that suits each one best.
Review content on a regular basis
Your BCP and recovery plan will not always be up-to-date. As soon as you start introducing new software and communication tools into your company, you’ll need new safety measures to safeguard this data. To ensure your plan is always up-to-date, make sure to review your BCP and recovery plans once every year.
Keep data security in mind
Data security should never be forgotten in your BCP. If your business falls prey to cyber-attacks such as ransomware, you may suffer damage that’s equal to or greater than a natural disaster. Recovery measures should be developed with cyber-attack risks in mind.
Take advantage of the cloud
Cloud solutions are an effective tool for BCP and recovery planning. With the cloud, you can take simple, affordable, and highly effective disaster countermeasures. For example, with Tsukaeru Cloud Backup, business data can be backed up safely in a data center away from the company. And with Tsukaeru Dokodemo Office, employees can continue work from home in the event of a disaster.
If you’re interested in advancing the BCP measures of your business but you don’t know where to start, we highly recommend using these cloud tools.
Learn more about Tsukaeru Cloud Backup here and Tsukaeru Dokodemo Office here.
And as always, please feel free to contact us.
A vast range of cyber attacks have been carried out against individuals and businesses in the modern age. Some of the worst to occur in recent years have been ransomware attacks. According to a report by the cybersecurity giant Symantec, the number of ransomware infections has increased every year since 2013. While attacks against individual users have declined since 2018, companies have seen a shocking 12% increase. To ensure everyone is fully informed, we’ll examine the catastrophic results of ransomware and identify potential prevention methods.
Big Companies Have Lost up to 5.6 Billion Yen to Ransomware Damage
It is well-known that ransomware attackers tend to target companies. They are, after all, more likely to pay a higher ransom for their precious data. A recent victim is the Norwegian aluminum manufacturer, Norsk Hydro. They endured a disastrous ransomware attack in March of this year, during which the company’s computer network was paralyzed. The result? An astounding loss of ¥5.6 billion.
What Exactly Happens During a Ransomware Infection?
At the time of infection, all employees will be unable to operate a company computer, and this includes opening files and folders. Instead, a message demanding for ransom will be displayed on the screen. Until it is paid, all work will become suspended. The most troubling possibility, however, is that data will not be recovered even after the ransom is paid. There is no guarantee that attackers will do as they say. In fact, there have been frequent cases where data was not recovered even after paying a hefty sum. For small and medium-sized enterprises, this data loss can ruin chances of business survival.
New Services are Preventing Attackers from Accessing Data
Since threats of ransomware have grown, many new services have begun to offer protection against data hijacking. Features tend to include access log monitoring, firewalls blocking suspicious activity, OS vulnerability detection, and virtual patch protection with no additional cost. Why not defend yourself against potentially irreversible damage and consider these anti-ransomware tools?
Prepare for Every Possible Outcome and Backup Data to the Cloud
It’s vital to take precautionary measures and protect against possible ransomware attacks, but it is equally important to back up our data on a daily basis. Should a ransomware attack occur, having a backup could mean the difference between staying afloat and failure. If attackers hold your data hostage, you won’t have to pay a ransom as long as data is stored elsewhere. Operations can be resumed immediately using your backed up data.
When considering ransomware protection, cloud backups are the most secure solution since they store data on external servers. Take a look at our Tsukaeru Cloud Backup service, fully-equipped with Active Protection, an artificial intelligence (AI) technology that safeguards against ransomware attacks. Should any problem arise, data restoration can be completed in just a few minutes.
Tsukaeru Cloud Backup
Contact Us