Small and medium-sized businesses around the world are suffering from a chronic shortage of workers, and in reaction, many businesses are implementing IT solutions to make up the difference. However, while this can improve productivity, it also increases cyber security risks. The more that a company relies on IT, the greater the possibility of damage or stoppage from cyber attacks. As a result, appropriate security measures are becoming even more important for small and medium-sized businesses.
Cyber security threats are on the rise
In March 2019, the Information-technology Promotion Agency, Japan (IPA), an independent administrative agency, revised its information security measures guidelines for small and medium-sized enterprises (SMEs) for the first time in more than two years. Referencing the increase of cyber security threats. IPA states that, "there are concerns that SMEs in the supply chain may be used as a foothold for targeted attacks on the companies they serve, and it is essential to take measures as soon as possible.” IPA also points out that SMEs often have less security awareness and inadequate measures compared to large companies and are therefore easier targets for attacks.
Cyber attacks: an ongoing problem
As an example of the threats that industries are facing, in 2017, the Osaka Chamber of Commerce and Industry (OCCI) surveyed SMEs with 50 or fewer employees, mainly in the construction, manufacturing, wholesale, and service industries. Out of 315 companies, 97, or nearly 30%, had been affected by cyber attacks, and among them, 22 companies, or 7% of all companies, had been infected by ransomware. In addition, a 2019 OCCI supply chain survey revealed that while the supply chain partners of one in four companies had experienced cyber-attacks, approximately 70% were unaware of their supply chain partners' cyber-attack preparedness or damage.
.jpg)
What is ransomware?
Recently, ransomware is becoming a growing problem for businesses, including SMEs. The word is created from the combination of the words “ransom” and “software,” and can also be described as “ransom malware.”
When a computer is infected with ransomware, the stored data will be encrypted or the computer itself will be disabled. It is basically impossible to access the data or computer unless cash or virtual currency is transferred to the attackers’ designated account to obtain the encryption key. When a ransomware infection occurs, not only the computer but also all data in other externally connected storage devices can be encrypted, potentially causing tremendous problems and loss for SMEs.
Cyber security vulnerabilities
Cyber attacks are usually conducted by exploiting security vulnerabilities, but what are these vulnerabilities exactly? Simply put, they are weaknesses in a program. Computer operating systems and software often contain programming and design errors and defects. Obviously, during the development process, programmers constantly check for these problems. However, some vulnerabilities do not become apparent until the software is actually released to the market.
Therefore, IT companies that provide operating systems and software will release information about the potential problems or software updates as soon as the vulnerability is identified. However, if a malicious third party creates an attack method that targets the vulnerability before the update, a company's data may be exposed to cyber attacks.
Common tactics and countermeasures
As the three main routes of ransomware infection are websites, links and attachments in emails, and USB flash drives, the following measures are recommended to protect your company’s data:
・Infection prevention measures
The first step is to be aware of the above three infection routes and implement basic precautions to protect your company's computers. Email attachments or links should not be opened carelessly, and if there is a security concern, ask the sender for confirmation or check the extension of the attached file. Extra caution should be taken with compressed file extensions (.zip, .rar, etc.). Also, USB drives should not be used casually, even in the office.
However, no matter the vigilance of each employee, it is impossible to protect your computers and systems from cyber attacks. Therefore, it is extremely important to always update your computer's OS to the latest version to reduce vulnerability. It also goes without saying that you should install virus software and keep it updated, as well.
・Damage mitigation measures in the case of infection
Even with the above precautions, a ransomware infection is still possible, and you should plan accordingly. With a good backup system, you can restore your data even if you experience an attack. If backing up to an external storage device, make sure that it is not connected to the system to avoid the spread of infection.
Security: What is the perfect backup?
A backup is the process of duplicating the data on your computer and storing it separately in case of data loss or other unexpected situations. So, what is the best way to actually backup your important data?
.jpg)
The "3-2-1" backup rule
In the backup world, it is said that in order to perfectly protect your data, you need to follow the "3-2-1 Rule.” Originally proposed in 2012 by US-CERT, a security organization run by the Cybersecurity & Infrastructure Security Agency, an operational component of the U.S. Department of Homeland Security, it was initially thought to be too time-consuming and impractical. However, as mentioned above, it is now being reevaluated as a rule to protect data from the growing frequency and sophistication of ransomware attacks in recent years.
The 3-2-1 rule refers to the following three rules:
・Create three backups
・Save backups in two different media
・Backup one copy to a remote location
Let's take a closer look at each of these rules.
Creating the backups
With only one or two backups, there is always a possibility that one or both may be lost or destroyed, as well as the original data. A third backup creates an extra layer of security.
Storing in two different media
If all of your data backups are in the same media, you could lose it all if the problem is related to the type of media. Storing it in a variety of media, such as DVD and hard disk, or tape and online, reduces the chance that one problem could wipe all your backups.
Backing up one copy to a remote location
What if your home or office catches fire? In Japan, earthquakes are relatively common, so it is possible that you could be affected by such a disaster. If all of your backups are in one place, they could be easily damaged or compromised. By keeping at least one backup in a remote location, you can be better prepared for different types of man-made and natural disasters.
Data protection with Tsukaeru Cloudbackup +
Cloud-based backup services are an excellent option that works perfectly with the 3-2-1 rule mentioned above. By storing your data in the cloud, your data will be backed up to a location separate from your physical office. It also stores your data virtually, providing a backup in a different media as compared to physical DVDs and hard drives.
We would like to introduce Tsukaeru Cloudbackup+, a cloud-based backup service from Tsukaeru.net. This innovative and reliable service is easy to set up, requires no capital investment, and backs up not only your files, but all your accounts, settings, and OS as well.
If you are considering a cloud-based backup service as part of your security measures, or if you are considering switching from your existing service, please contact us below.
Click here for more information on Tsukaeru Cloudbackup +.
.jpg)
Call toll-free: 0120-961-166
Office hours: 10:00-17:00
To improve your company’s performance, improving business efficiency is an important step. One of the best ways to maximize that efficiency is through the smart use of IT tools.
In any industry, cloud computing is now essential, but only approximately 30% of companies use it for data backup. In this article, we’ll take a look at cloud backup, not only an effective time saver but also excellent disaster preparation.
Effective time saving tools
According to the Japanese Ministry of Internal Affairs and Communications survey on telecommunications usage trends for fiscal year 2019, 64.7% of all companies in Japan use cloud services. The most common use was for file storage and data sharing, an efficient way to save time as compared to the traditional use of paper-based files and email attachments.
While there are many tools to improve business efficiency and productivity, it is important to clearly define the purpose of their introduction. If just based on the vague concept of "saving time," the results may not be worth the effort to implement the tool.
BCP(Business Continuity Plan) and DR(Disaster Recovery)
Data backup is another reason for adopting cloud services. According to the survey mentioned above, 31.4% of all companies in Japan use cloud services for this purpose, not only to protect against human error, but also as risk management for large-scale disasters. Cloud-based backups should be part of your business continuity plan (BCP), allowing your company to continue or quickly recover its core business while minimizing damage when faced with a natural or man-made disaster.
DR (Disaster Recovery) is a similar concept to BCP, but it differs in that BCP focuses on the whole business, while DR focuses on the recovery and restoration of data and computer systems that have been affected by disasters or terrorist attacks. Think of BCP as an umbrella plan and of DR as part of that plan.
What is Disaster Recovery (DR)?
As mentioned above, disaster recovery refers to the recovery of data and systems that have been affected by a disaster, as well as the policies and procedures to be taken.
The key elements in DR are RPO (Recovery Point Objective) and RTO (Recovery Time Objective).
As briefly mentioned in a previous article on backup testing, RPO is an indicator of the maximum length of time in which data might be lost when restoring your system after a disaster. For example, if the RPO is set at 0 seconds, data loss will be avoided regardless of when the disaster occurs. However, if the RPO is set as the previous backup, all data from the most recent backup until the time of the disaster will be lost.
In contrast, RTO refers to the maximum acceptable time that your systems can be down after a disaster. For disaster recovery, the shorter the RTO, the better. For example, if the RTO is set to one hour, data and system recovery must be completed within one hour of the disaster occuring.
.jpg)
Why is DR necessary?
As more IT tools are used to improve business efficiency, so does the amount of important company information stored in the system as data. The impact of a huge data loss due to a disaster or the inability to access the system for an extended period of time can be immeasurable.
According to Infrascale's Disaster Recovery Statistics (2015), one hour of downtime can cost a small business $8,000, a medium business $74,000, and a large business $700,000. Companies without a DR plan in place may be forced to suspend business, thus lose the trust of customers and suppliers, and may be exposed to information leakage risks.
Case Study (Europe): Post-fire data restoration through DR implementation
On March 10, 2021, a fire broke out at one of OVHcloud’s four large data centers in Strasbourg, France, located along the Rhine River. As a major European cloud service company with more than 1.5 million customers worldwide, it is easy to imagine the amount of data that OVHcloud was managing.
Immediately after the fire, the company announced their recovery plan and had their servers up and running again 10 days later. Although some data was lost due to the fire, the company was able to minimize the damage due to its DR planning during normal times.
How to select the best system for DR measures
In terms of DR effectiveness and cost, there are two major types of systems for consideration.
1.Tape drive backup (cost: high, RTO: very long)
As the name implies, this is a method of backing up data on a "tape" drive. The main advantage is that it is easy to move data as it is stored on a physical medium. However, it is necessary to consider the environmental conditions for storage and the operational costs involved, such as follows:
・Room temperature and humidity must be strictly controlled, requiring a storage location with proper environmental controls outside the office.
・It can take time to access or download data.
・The complexity of such a system requires more expertise and specialized equipment than other backup methods, resulting in higher maintenance costs.
When trying to restore data stored on tapes, it is possible that data may be lost due to poor storage conditions. Also, repeated physical handling may damage tapes which can cause data loss.
Because of these concerns, backups to external disks or the cloud are becoming the mainstream as new alternatives to tape.
.jpg)
2. Remote network backup (cost: high, RTO: short)
A second method is to back up data to a different location through a network. This is effective for DR as backup data are stored in a separate location from the main data. In addition, although the restoration process still requires a restore, RTO can be kept to a shorter time compared to tape media.
However, the cost is usually higher because a separate backup location must be maintained by the company.
.jpg)
The importance of data replication
Data replication creates a backup system from the original data, allowing for an immediate switchover in the event of a failure. This can be considered as a “duplication" of the system. This backup system will continue to operate at all times, an extremely effective DR solution from the perspective of RPO.
However, this replication can be very costly if you create and maintain the system yourself; it could cost as much as operating your main system. Also, if the main data are affected by a virus, it will be replicated directly into the backup system.
Tsukaeru Cloud Backup + features and benefits (cost: low, RTO: short)
Tsukaeru Cloud Backup + automatically backs up the entire system according to the customer’s settings. As a cloud-based backup, no hardware or other equipment is required, lowering the initial and operation costs.
In general, the cost of implementing data replication as a DR solution is quite high. However, Tsukaeru Cloud Backup + minimizes the cost of maintaining duplicate systems through system replication while also reducing RTO to an incredibly short period of time.
Tsukaeru Cloud Backup +: The low-cost, labor-saving solution
Protect your data at the low cost of 30 JPY per day/0.98 JPY per 1.0 GB, depending on the capacity you need. Also, as a cloud-based backup, there is no need for specialized IT or security knowledge or complicated setting management. Furthermore, since the entire system image is backed up at once, backup time can be significantly reduced compared to normal file backup.
Cloud Backup + is available to try for free for 30 days, so please consider trying it out to see if it fits your DR needs.
Click here for more information on Tsukaeru Cloud Backup + (Plus).
.jpg)
Call toll-free: 0120-961-166
Office hours: 10:00-17:00
The Internet, social media, and smartphones have all become integral parts of our lives. We can keep in touch with our friends, check the news, go shopping, etc. However, while this may make our daily lives more convenient, there are some new problems that have appeared. One of the most significant ones is "online privacy.”
Is your online privacy really safe?
As the Internet becomes more and more integrated into our society, online privacy is becoming just as important as privacy in real life.
For example, if your online shopping account password is revealed to a third party, your personal information such as credit card number and home address could be at risk. Even without a password leak, there is still a possibility that you could be identified from the photos and information you post on social media or even be a victim of online stalking.
Growing global interest in personal data privacy protection
More recently, internet users’ concerns about personal data being collected by websites and online advertisers have been on the rise worldwide. Most websites and social media sites collect data such as user demographics and website page browsing history for targeted advertising and other purposes. To guard against potential problems, there are specific actions that internet users can take.
.jpg)
Seven steps to protect your data privacy
So, what can an individual do to better protect online data privacy? Here are seven ideas to help you do just that.
1. Set a strong password
Create and use a complex password with a combination of letters and numbers at a minimum. A mix of uppercase and lowercase letters, numbers, and symbols is even more effective.
2. Don’t use the same password for multiple sites
If you use the same password for multiple sites, all of them are at risk if one is compromised. Even if you have a basic password and use only one different character for each site, this is much safer than using the exact same password. If you can't remember that many passwords, there are many free and paid password managers you can use.
3. Think before clicking "I agree"
When visiting a website for the first time or installing an app, you often see a message about the "Privacy Policy" or "Data Collection Policy," Do you usually just click "I agree" without considering what it means? While it may take more time, you would be wise to take a look at the policies of that site or app. Increasing your awareness of online privacy on a regular basis will help you protect your personal information.
4. Review your privacy settings
Recently, many social media and search services have begun to offer detailed "Privacy Settings" management screens. It is highly recommended that you check and review the privacy settings and details for each and every item.
.jpg)
5. Review your social networking use
Do you usually casually post information about yourself, your neighborhood, your children, etc. on social media? Although major social networking sites such as Facebook and Instagram have taken measures such as automatically removing location information from posted photos, it is still possible to discover personal information from what you post. You should always keep in mind that people other than your friends and followers may see your posts and be cautious when posting.
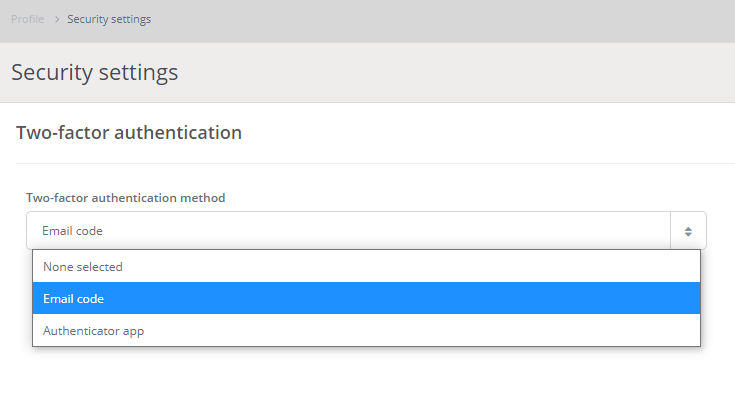
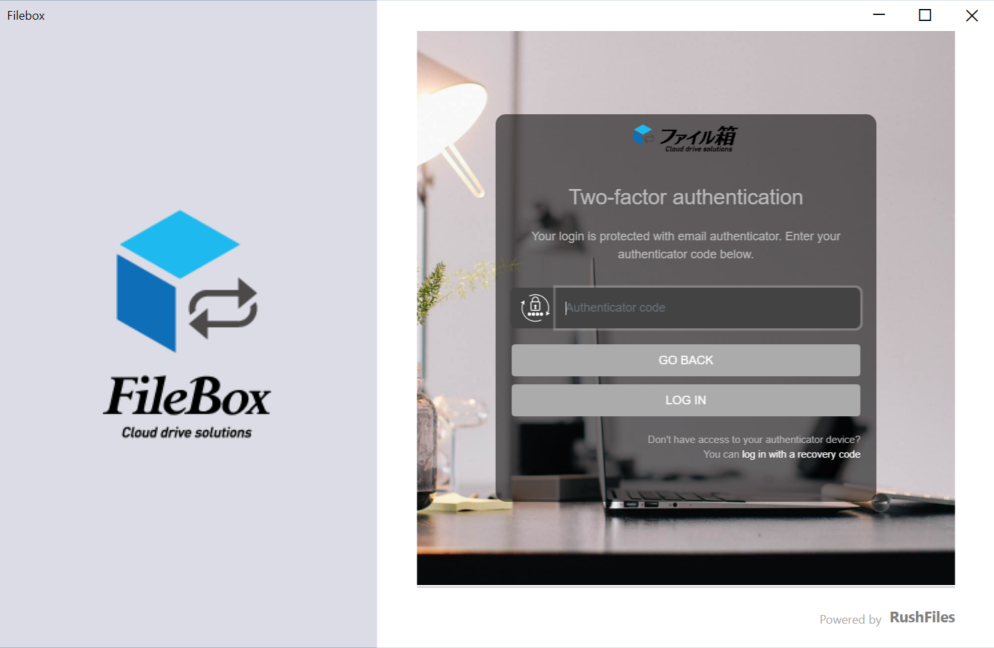
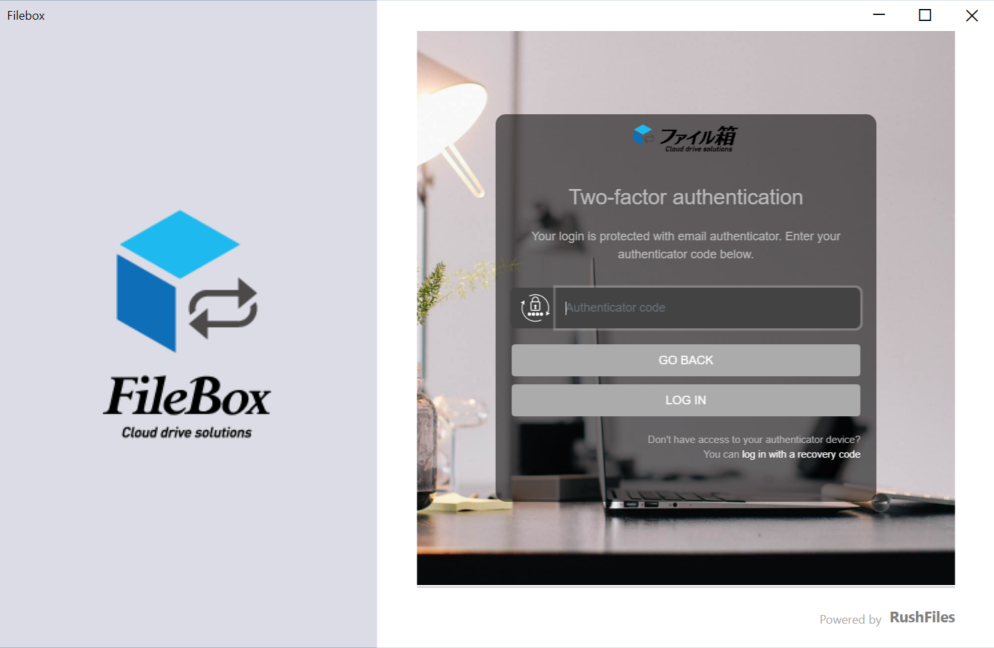
6. Use two-factor authentication
More and more services are offering a two-factor authentication option that combines not only password entry but also email, SMS, or app authentication. With two-factor authentication enabled, even if your password is compromised for some reason, the risk of someone stealing your personal information or logging in illegally is greatly reduced.
Two-factor authentication has also been implemented in the Tsukaeru cloud service to protect the personal information of our customers.
7. Make it a habit to back up data
In the end, you are responsible for protecting your online privacy and digital data! However, it shouldn’t be something that you need to remember to do! Taking actions to protect your data on a regular basis should be a habit, especially for files, folders, and information that you use for work. It is very important to back them up properly to be prepared for unforeseen circumstances.
Choosing the right backup solution for you
When it comes to backup solutions, an essential component of data protection, the most important thing is to choose a solution with security and peace of mind. Tsukaeru Cloud Backup combines simplicity of use with the highest level of state-of-the-art security to create the perfect service for business backups. The all-in-one solution Tsukaeru Cloud Backup + (Plus), which integrates backup functions with security management tools, is also becoming more popular. Please visit the links below to learn more.
Click here for details of the Tsukaeru Cloud Backup service.
Click here for details about Tsukaeru Cloud Backup + (Plus).
.jpg)
Call toll-free: 0120-961-166
Office hours: 10:00-17:00
Daily backups are essential for protecting corporate data. They are an important part of ensuring that business can continue as normal even in the event of unexpected situations such as natural disasters or PC problems.
However, did you know that just making backups is not enough for the minimum BCP (Business Continuity Plan) and DR (Disaster Recovery) measures? In this article, we will introduce the concept of backup testing (restore testing) that should be considered in conjunction with regular backups.
What is backup testing?
Backup testing refers to testing and confirming during normal operations whether or not the backed-up data can be properly restored.
Even if data is backed up regularly and correctly, it will be meaningless if the backed-up files and folders cannot be restored in an emergency.
It's easy to think, "I always back up my data, so I'm fine." However, not surprisingly, problems can still occur. In fact, approximately 1/3 of all companies experience difficulties when restoring from backup data.
Why are backup tests necessary?
As evidenced by the recent COVID-19 pandemic, unforeseen events can affect businesses and society. As Japan regularly experiences earthquakes and typhoons, it is important to be prepared for all contingencies.
Under such circumstances, data and system backups are now becoming an essential part of corporate risk management. However, while most companies have backups, many have not actually tested them.
Without a backup test, there is no way to know if your data can be restored in a crisis. If it cannot be restored, not only will all the time and money spent on backups be wasted, but for small and medium-sized companies and startups, there is also a risk that it will directly lead to a business continuity crisis.
In order to make your regular backups truly meaningful, backup testing is an extremely important task that should not be neglected.
.jpg)
What is checked in a backup test?
In the backup test, it is important to check not only whether the backed-up data can be restored without any problems, but also whether the assumed RPO (recovery point objective) and RTO (recovery time objective) can be met.
RPO is expressed as a time measurement from the loss event to the most recent preceding backup. In other words, it refers to the amount of time that has passed since the last backup. For example, if you make regular backups every day, your RPO is 24 hours. In the event of an incident, data modified or newly created after the latest backup will be lost. With a backup test, it is necessary to confirm whether the data saved at the RPO point and set in advance can be restored properly.
On the other hand, RTO refers to how much time (targeted valued) an application can be down without causing significant damage to the business. For example, if you decide that three hours is the maximum downtime that is acceptable for your company, then your RTO is three hours. Businesses must determine what is an acceptable RTO and plan accordingly. A backup test will confirm if the determined RTO can be met.
How often should backup tests be performed?
Only performing backup tests occasionally and randomly is insufficient and dangerous for business. In order to ensure the effectiveness of backups and backup tests, it is essential to conduct tests on a regular basis. If possible, try to run backup tests at least once a month or so.
However, conducting a backup test for all the data every month can be a burden on your resources. Therefore, it is recommended to perform a partial restore test of particularly important or high-risk data on a monthly basis, and a complete restore test of all data on a semi-annual or annual basis.
Why is the cloud the best choice for backup?
In regards to backups, until a few years ago, site backups were the norm, saving data to an internal server. However, in the past few years, more and more small and medium-sized businesses, as well as large corporations, have been making the transition to cloud backup. For the following advantages, it is gaining popularity as a smart choice for today's times:
• Secure against ransomware or other malware attacks
• Protected from natural disasters or power outages
• No need to maintain and update backup servers
• Extremely easy to set up – even a novice
• Highly reliable
Tsukaeru Cloud Backup is affordable and easy to use!
The Tsukaeru Cloud Backup service provided by Tsukaeru.net is a complete cloud-based backup solution that can be easily introduced without the need for extra equipment or initial costs. This high-quality cloud backup service is easy to use, safe, and affordable and has been well received by our clients nationwide.
• Simple: Protects all data, including OS, with just five minutes of setup.
• Secure: Data is encrypted with AES-256 in your environment and transferred with AES-256.
• Affordable: Data protection measures start from 30 JPY per day/0.98 JPY per 1GB regardless of how much space you need.
A 30-day free trial is currently available, allowing you to experience all the benefits of cloud backup without any cost. To find out more, please contact us using the form or call us at the telephone number below.
If you are in the IT industry, you have to have heard the word "backup" at least once. And lately, you have definitely been hearing the term "cloud backup" more and more.
Think about your own situation. When was the last time you backed up the data on the computer in front of you?
Sometimes problems come out of the blue
-scaled.jpg)
It’s a typical morning. You arrive at the office and turn on the computer…
But what if your computer suddenly won't start up? Or later when you're in the middle of writing a report in MS Word, your computer crashes and automatically reboots?
Many of us have experienced these kinds of problems in our daily life or at work. These things just happen.
While we all hope this does not happen to us, unexpected problems like those above are not uncommon. In addition to computer crashes, there are many other possible situations, such as data transfer failure, file loss, or batteries finally running out of power. When these things happen, valuable data can be lost.
Backup basics
.jpg)
Backing up is the process of duplicating or copying the data on your computer in case something goes wrong. This is especially important for large files that take a long time to create. It is a good idea to keep copies in several different locations, such as on an external hard drive, USB, or in the cloud.
Microsoft Office applications also have an auto-save function that can be utilized if necessary.
If you haven't paid much attention to this up now, you should definitely start with these following steps to protect your important data.
1.Choose and begin using a backup method, such as mentioned above.
2.For manual backups, create and follow a backup schedule.
3.When using Microsoft Word, make sure autosave is enabled.
What is cloud backup?
"But backing up is such a pain…”
There are many such people in the world. This is where the importance of cloud backup becomes apparent.
Cloud backup is a method of backing up your files and data to a cloud-based server or storage space on the Internet. Since it is not a physical backup, there is no need to use your own USB memory stick or external hard drive or to set up an internal backup server. All you have to do is sign up for a cloud backup service, complete the initial setup, and you're good to go.
Cloud backup benefits

Let's take a moment to review the good points of cloud backup.
Simple and easy
Setting up and using cloud backup is, above all, incredibly easy to do. All you need to do is register with the service, install the software, set up the initial settings (and regular backup settings), and then the software will back up your files and folders to the secure cloud storage all on its own.
Relatively low price means cost savings
While there is a monthly fee, there are no large initial investments needed to create a server or expenses to deal with unexpected server problems, keeping the overall costs usually much lower. This is a perfect solution for those who want to keep backups but also want to save money.
Corporate services provide security
Corporate cloud backup services generally offer better security measures than services for individuals.
Cloud backup disadvantages
Of course, cloud backup is not always the best solution for all situations. Be sure to keep these potential issues in mind when examining your options.
Internet connection required
As cloud backups utilize their servers via the Internet, they need to be connected to back up files and data. Also, it is not just enough to be connected to the Internet; a stable and fast connection is necessary to some extent.
Slow backup speeds
Depending on a company's Internet environment, backup speeds may be slower than when backing up to a local server or other location within the company.
Is cloud backup the new norm?
Cloud backup has both advantages and disadvantages, but in recent years, its adoption is gradually increasing among small and medium-sized companies. It may soon become a mainstream backup method for companies in the future, as it is perfectly compatible with remote work.
Protect your files and data with Tsukaeru Cloud Backup
Tsukaeru Cloud Backup is a revolutionary cloud-based backup service that allows you to back up all the applications, files, accounts, settings, and even the OS on your computers without the need for any capital investment. This service is popular for its easy setup and usage, a low cost of 30 yen per day/1GB from 0.98 yen per day, and a focus on security measures.
If you are in the market for backup or cloud services, or are considering switching from an existing service, please feel free to contact us to learn more.
As an added incentive, we are currently offering a 30-day free trial!
Click here for details on Tsukaeru Cloud Backup.
Contact us at Tsukaeru.
In November 2020, the Japanese government's Minister of Digital Transformation, Takuya Hirai, announced that the Cabinet Office would discontinue the use of password-protected zip file email attachments (PPAP) for security reasons.
In today’s article, we will provide an overview of PPAP, its problems, and safe alternatives.
What is PPAP?
.jpg)
PPAP refers to the process of sending an encrypted file (with password) attachment in an email and then sending the password to unzip the file in a second email. As a part of security measures, this method is used by many companies and organizations, as well as government agencies in Japan.
The abbreviation "PPAP" was coined by IT consultant, Akira Ootaishi, and comes from the following terms (*1):
-
P: Password-protected file is sent.
-
P: Password is sent separately.
-
A: Encryption (“angouka” in Japanese)
-
P: Protocol
Do other countries use PPAP, or is it only used in Japan?
.jpg)
While PPAP is a common security measure in Japanese companies, in fact, it is rarely seen overseas where password-protected zip files tend to be viewed suspiciously and treated as potential virus vectors.
It is not clear why PPAP has become so popular in Japan, but it seems to be one of the unique business practices that have developed in Japan.
The history of PPAP
PPAP is widely used in Japanese companies, and in many cases, its use is even an official company security policy.
The origins of this practice can be traced back to the early days when email was first used for business purposes, and this method of sending password-encrypted zipped files by email and then providing the password through another channel (fax, paper document, etc.) was developed as a security measure.
The above method was thought to be useful in becoming a Privacy Mark certified entity and spread rapidly in Japan. However, faxing or sending paper documents became too cumbersome, so it was gradually decided that passwords could also be sent by email, simplifying the method. As a result, the use of PPAP in Japan has remained unchanged to this day.
Why is PPAP dangerous? Why is it being abolished by the Japanese government?
As mentioned at the beginning of this article, the Cabinet Office has decided to abolish the use of PPAP. (*2) In response, the Japan Institute for Promotion of Digital Economy and Community (JIPDEC), which operates the Privacy Mark system, has also officially announced the organization has never endorsed PPAP. (*3)
However, why is PPAP considered dangerous, and why is there a growing trend to abolish it? Below are five reasons:
▼ Sending encrypted zip and password separately by email provides limited protection.
There is little point in sending a password-protected zip file and the password in separate emails if hackers can access the email system. If the first email with the attachment is accessible, the second email with the password will be equally compromised.
▼ Security software cannot detect viruses in attachments.
Currently, many security software programs automatically scan email attachments for viruses. However, if the attached file is zipped and encrypted, security software will not be able to check the contents. In other words, if the file contains a virus, it is likely to be delivered to your inbox undetected.
.jpg)
▼ Zip files encrypted with passwords are at high risk of compromise.
Passwords-encrypted zip files are considered in the industry to be relatively simple to crack. Unlike website logins, encrypted zip files are easy for cybercriminals to access because unlimited password attempts are allowed.
▼ Emails may be vulnerable to interception or access in transit.
Emails pass through multiple servers between the time it is sent and received by the final party. If any part of an email is not properly encrypted, an attacker can easily eavesdrop on the contents. Therefore, passwords written in plain text are extremely dangerous.
▼ Wasteful measures reduce work efficiency
The PPAP process requires a great deal of time and effort on both the part of the sender and the receiver. Multiple steps are necessary to create and send the encrypted file by the sender. The receiver has to access the PPAP system via the first email, then open the second email to copy and paste the password. This inefficiency can result in a decrease in productivity.
Alternatives to PPAP
.jpg)
Let us look at an alternative to PPAP for businesses to send and receive files securely.
▼ Cloud storage is the safest measure.
The most secure alternative to PPAP, and one that is actually used most often, is the use of cloud storage to send and receive files. With cloud storage, specifically, files are often shared in the way described below.
For this article, we will use our Tsukaeru Filebako cloud file sharing service (client version) as an example.

After installing the Tsukaeru Filebako desktop client, files can be easily shared in the familiar Explorer format.
The beta version, scheduled for an early 2021 release, will allow passwords to be added to public links directly from Explorer, without having to access the browser version (web version).
1.Right-click on the file name to share and then select “Create Public Link.”
2.The password can be directly entered in the pop-up window that appears.
The password-protected file can be easily shared by providing the recipient with the created link.
The ability to share files via URLs with cloud storage solves all of the potential PPAP problems. There is no need to encrypt the file each time they are sent or send multiple emails.
▼ 2FA (two-factor authentication) settings provide even greater security.
Recently, two-factor authentication has been increasingly implemented as a security measure to prevent identity theft and unauthorized logins. In the past, users were only authenticated with an ID and password when logging in. However, now, another level of authentication is being added to strengthen the identification process.
Of course, this two-factor authentication feature is also available with Tsukaeru Filebako.
To implement, select “Security” then “Two-Factor Authentication” from the settings screen, and choose between "Email Address" or "Application."
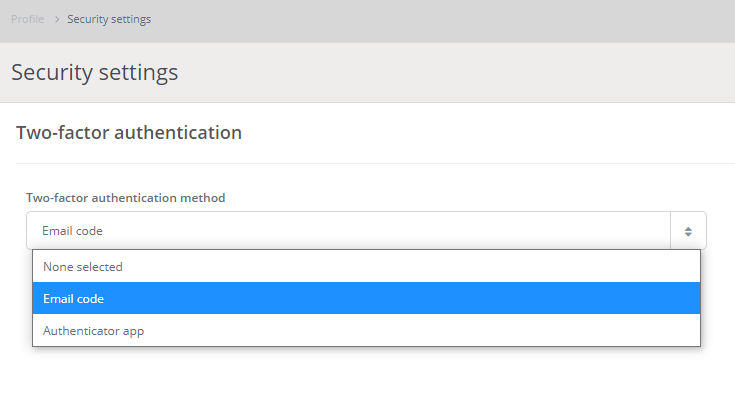
If email address authentication is chosen, recipients will receive by email the authentication code needed to log in.
▼ Tsukaeru Filebako provides reliable security.
When choosing a cloud storage service, robust security measures are extremely important. For this reason, we recommend Tsukaeru Filebako, the cloud storage service from Tsukaeru mentioned earlier.
Tsukaeru Filebako is a full security, cloud storage service that is hosted on its own servers in Japan and allows the setting of expiration dates for shared links and the remote deletion of device data. It can be installed on the same day, is easy to use even for beginners, and has an affordable and simple fee structure.
A two-week free trial is also available (completely free of charge with no need to sign a contract!). Please take advantage of this opportunity to try it out for yourself.
Click here for Tsukaeru Filebako details.
Sign up for a free Tsukaeru Filebako trial.
Contact us at Tsukaeru.
<Sources>
*1 Workplace Reform Starting with Changing the Habit of Attaching Files to Emails (PDF, Japan Institute for Promotion of Digital Economy and Community)
2* Automatic Encryption ZIP Files Discontinued by Cabinet Office; Cabinet Secretariat – Digital Minister: "Inappropriate" (Nihon Keizai Newspaper)
*3 Sending files as email attachments (Japan Information Processing Development Corporation)
With the increasing spread of digital transformation and remote work, cybersecurity is becoming even more important. One particularly alarming and growing risk is the threat of ransomware.
Ransomware damage has increased 15-fold in just two years
Ransomware is a powerful malware that can infect PCs and spread to a company network, making all data unreadable. The normal tactic of attackers is to threaten the complete and irreparable destruction of data if a specified ransom is not paid by the deadline.
According to a report by Cybersecurity Ventures, global ransomware damage was around $325 million in 2015. However, by 2017, it had grown 15 times that amount to approximately $5 billion. At this rate, it is predicted to reach $20 billion by 2021. This is one of the highest rates of expansion among all cybercrimes, and various media, industry leaders, security companies, and cyber-attack experts confirm that the above prediction is likely to be correct.
With an attack every 11 seconds, ransomware is becoming a mainstream cyber-attack
Because it is relatively easy to implement and the returns are great, ransomware is quickly developing into a common problem around the world, including Japan.
In 2016, the attack rate was once every 40 seconds, and the number of companies affected by ransomware has only continued to grow. It is estimated that in 2021, the pace will accelerate to the point where every 11 seconds a company will experience a ransomware incident.
Once infected, data recovery is difficult
The trouble with ransomware is that once infected, complete data recovery is often impossible. There is no guarantee that data will be returned even if the ransom is paid.
In fact, it is reported that in most cases, the ransom was paid, but the data was already destroyed and could not be recovered. Moreover, the ransom demanded by the attackers is increasing more and more every year.
Education x Cloud: Two Approaches to Ransomware Protection
Let’s look at some possible losses from a ransomware attack:
・Loss of important business data and customer documents
・Loss of public trust
・Suspension of normal business operations (for several days to several weeks)
For small and medium-sized enterprises and businesses, pre-emptive ransomware protection is very important.
Effective ransomware countermeasures should take a two-pronged approach: the human side and the software side.
The term “human side” refers to the education and training of employees. The vector of ransomware infection is usually email. Regular and ongoing employee education about tips and tricks for identifying malicious emails and the risks of ransomware is simple, yet extremely effective.
On the “software side,” in addition to installing ransomware-compatible security software, it is important to incorporate a solution that can safely back up data in case of an emergency. With cloud backup, all data is stored on a secure cloud server that is separate from the company's network, providing assurance even if a ransomware infection occurs.
The best in ransomware protection from Tsukaeru Cloud Backup + (Plus)!
Tsukaeru Cloud Backup+ is a popular service that is ideal for ransomware protection. Easy to implement, it provides a simple and powerful all-in-one solution.
Tsukaeru Cloud Backup+ features are as follows:
・Centralized security measure and backup management in a single service
・Latest AI-incorporated ransomware countermeasures
・Comprehensive cybersecurity measures with an easy-to-understand management screen
・Secure cloud backup file and data protection
It’s never too late to start playing it safe.
By the time a ransomware infection is identified and panic sets in, it's too late. As remote work continues to be a major issue in 2021, the possibility of more attacks and even more dangerous variations will not disappear anytime soon.
If you have any questions, please feel free to contact us by phone or email. A free trial service is also available!
Click here for more information about Tsukaeru Cloud Backup+.
Contact us at Tsukaeru.
Toll-free number: 0120-961-166 (Office hours: 10:00 – 17:00)
Reference: https://cybersecurityventures.com/global-ransomware-damage-costs-predicted-to-reach-20-billion-usd-by-2021/
The COVID-19 pandemic has brought renewed attention to the importance of business continuity planning (BCP). In this article, we will explain the significance of BCP for small and medium-sized businesses and why cloud solutions are recommended for BCP implementation.
What is BCP? Why is it essential for small and medium-sized companies?
BCP (Business Continuity Plan) refers to plans and measures that are formulated in advance so that business activities can be quickly resumed in the event of a disaster, cyber attack, or other contingency.
With proper BCP measures, business operations can be continued without delay even in the event of unforeseen circumstances such as the following:
・Natural disasters such as massive earthquakes and floods
・Cyber attacks such as ransomware
・Fires in offices and other business locations
・Prolonged pandemics
Without BCP in place, it will be difficult to quickly restore and resume operations in the event of the above problems or disasters due to issues such as the loss of important documents and data necessary, damage to internal servers and computer systems that will take time to repair, or unusable or unsecure office space. This can result in a loss of trust from business partners, customers, and consumers, a risk that a small or medium-sized company or startup cannot accept.
While many people have the perception that BCP is something only for large companies, in fact, it is important for small and medium-sized enterprises (SMEs) with concerns regarding their management capabilities to prepare for and respond to emergencies.
In fact, both the 2011 Great East Japan Earthquake and the recent pandemic conditions have caused a series of bankruptcies among SMEs in Japan, highlighting the importance of emergency preparedness.
Cloud computing: The best BCP choice for SMEs
One common obstacle for SME implementation of BCP measures are budget and time constraints. This is why we recommend a BCP cloud solution.
Implementing a cloud solution as part of your BCP offers the following advantages:
・Data can be quickly recovered from the secure cloud server if computers or systems are damaged.
・Remote work can be easily implemented if the physical office space is damaged or compromised.
In addition, cloud-based BCP measures are inexpensive and affordable, can be implemented immediately, and do not require specialized knowledge or complicated settings, all of which makes them relatively easy to implement with limited time and investment capital.
The Tokyo Metropolitan Government has been offering BCP promotion subsidies for some time. However, the subsidy rate has been increased for the sixth round of applications in January 2021 in order to subsidize the cost of required BCP equipment, including countermeasures against infectious diseases such as COVID-19. These subsidies also include cloud servers and backup systems for data management due to loss of business premises or inability to come to work.
Easy and affordable crisis management with Tsukaeru Cloud Backup+
Tsukaeru Cloud Backup+, a cloud solution from Tsukaeru.net, is a new service recommended for implementing BCP measures for small and medium-sized businesses. The introduction of this service makes it possible to simply and centrally manage security measures and data backup, key elements of effective and efficient BCP. As a cloud service, there is no need for huge initial or capital investments.
Tsukeru Cloud Backup+ features
・Securely backs up applications, systems, and data on any device
・Fast and reliable restore function
・Advanced ransomware and malware protection based on the latest AI
・Intuitive operation with easy-to-understand management screen
・Simple and centralized management of all devices
・Save time and money by remotely managing end-user devices
・Visualize hard disk status in advance and predict problems before they occur
To experience all the Tsukaeru Cloud Backup+ can offer, please feel free to contact us for a free trial.
Click here for more information about Tsukaeru Cloud Backup+
Contact us at Tsukaeru
As the COVID-19 crisis drags on, many companies are continuing to rely on remote work more and more. While it is becoming more and more popular as it can lead to a better work-life balance, recently, "remote work fatigue" is becoming a common problem.
Remote work productivity: Japan is the worst!
Last month (November 2020), Oracle released an interesting study (*1) on the state of remote work around the world in the wake of the COVID-19 pandemic. According to the survey, the rapid growth of remote work and the reduction of commute times has increased the number of hours worked in many countries. However, the opposite is true in Japan, where 34% of respondents said that their work hours have decreased (21% increased).
In addition, 46% of Japanese respondents said that the COVID-19 pandemic caused a decrease in productivity, significantly higher than the 15% who reported an increase in productivity. This is in stark contrast to the majority of people in most other countries who say their productivity has increased.
The power of technology to improve remote work operational efficiency
Various factors have been identified for the slow increase in remote work productivity in Japan, such as the need for experts in the subject matter to work closely together or the difficulty in creating environments in the family home that allow for concentration on work matters.
Technology, especially the cloud, is gaining attention as a means of improving remote work efficiency as of late. In fact, this prolonged remote work period has led to a rapid increase in the introduction of cloud storage and business communication tools that are ideal for remote collaboration in Japan.
Tsukaeru FileBako is ideal for remote work collaboration
Tsukaeru FileBako is the perfect solution for improving productivity and collaboration in remote work. Files are stored on a cloud server rather than in a local environment, making them accessible anytime, anywhere, and from any device, all with industry-leading security. Internal file transfers can be completed in seconds, without the need for email attachments.
For more information on the features and benefits of Tsukaeru FileBako, please check out the service details page below. We're also currently running a 30% off offer until December 22, 2020, so feel free to contact us!
Click here for more information on the Tsukaeru FileBako service.
Click here for details of the Tsukaeru FileBako 30% off campaign (until December 22, 2020)
Tsukaeru will also be hosting a free webinar on December 10 and 11, 2020, a must-attend event for anyone considering implementing cloud services. This webinar will also include case studies of Tsukaeru FileBako, so please join us if you are interested.
Click here for more information and to register for the free webinar!
Contact us at Tsukaeru
(*1) : “AI@Work” survey – Oracle Japan
In the wake of the COVID-19 global pandemic, online and digital are becoming increasingly important to business. While these trends have many advantages in terms of new ways of working and other aspects, it is also true that cyber attacks (i.e., ransomware and malware) are rapidly increasing to exploit the gaps.
Ransomware attacks are on the rise
A type of cyber attack called "ransomware" is particularly risky at the moment. This attack is a virus that encrypts files on an infected PC and makes them unreadable to the owner(s).
Ransomware attackers demand a "ransom" from their victims. If the ransom is paid, they will unencrypt the files and restore them to their original state.
There are currently many different types of ransomware, such as WannaCry, which came on the scene around 2017. This year, a new ransomware called MAZE has become a global epidemic, and the damage is slowly becoming more noticeable in Japan, as well.
Problems with ransomware countermeasures
The difficulty with ransomware countermeasures can be summed up in two points: the modus operandi has become so sophisticated that it is difficult to prevent infection, and once infected, the probability of regaining access to data is low.
Ransomware is currently the most popular method "chosen" by attackers, and the techniques and methods are evolving every day. Although the main route of infection is through links and attachments in spam e-mails, it is often difficult to guard against the attack because the e-mails look completely normal, for example, identical to ones from trusted business partners.
Also, once infected with ransomware, it is very difficult to recover the encrypted files. Even if you pay the "ransom" demanded by the attackers, there is no guarantee that your data will be restored. Unfortunately, there have been many cases where the ransom was paid in full, but the encryption was not lifted. In the end, the victims had no choice but to give up on the lost data and move on.
Tsukaeru Cloud Backup+ Ransomware Protection: a breakthrough service!
Tsukaeru Cloud Backup + (Plus), recently released by Tsukaeru, is a groundbreaking service developed specifically to address the growing risk of ransomware and malware.
▼Cloud backup means you don't have to worry if you get infected
Tsukaeru Cloud Backup+ is a comprehensive solution that integrates a backup function and security measures, regularly backing up all of your PC data to a secure cloud server. In this way, even if your company's local PC is infected with ransomware, all you have to do is restore from the pre-infection files from the cloud.
▼Next-generation AI-based ransomware detection
Tsukaeru Cloud Backup+ includes the latest next-generation ransomware and malware detection, which uses AI technology to detect and block unknown threats to prevent ransomware infections with overwhelmingly high probability and accuracy.
▼All-in-one security measures necessary for today's world
Tsukaeru Cloud Backup+ includes a whole host of security features that are crucial in this day and age, including automatic virus scanning, vulnerability testing, patch management, malware quarantine, and more. There’s no longer any need to juggle multiple tools for backups and security measures.
To learn more about Tsukaeru Cloud Backup+, please feel free to contact us at your convenience.
Click here for more information about Tsukaeru Cloud Backup+.
Contact us at Tsukaeru.


.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
-scaled.jpg)
.jpg)

.jpg)
.jpg)
.jpg)
.jpg)