According to the results of a survey released in March 2022, the domestic public cloud service market in 2021 was 1.5879 trillion JPY, up 28.5% from the previous year. Even more remarkable is that the market is expected to grow to 3.7586 trillion JPY by 2026, approximately 2.4 times the 2021 level.
One reason for this incredible growth is that many companies are shifting their backup storage operations to the cloud. However, that does not mean everything is safe. Companies need to understand the risks and disadvantages, as well as the benefits, of cloud backup in order to be prepared for whatever the future holds.
In this article, we will focus on the disadvantages of cloud backup and explain which companies are suited for cloud backup and which are not.
What are the disadvantages of cloud backup?
While cloud storage has a number of benefits – a reduced need for onsite hard drives and greater storage capacity among others, there are also some disadvantages. These include the following:
Running Costs
Cloud backup can reduce operation and maintenance costs, particularly when it comes to initial setup costs, staff time, and construction.
However, cloud backup has a fixed monthly cost, and depending on the services that are best for your operation, this can be high.
Operations and Security are the Provider’s Responsibility
According to the Ministry of Internal Affairs and Communications' White Paper on Information and Communications (2020 edition), the second most common reason for companies not using the cloud is "security concerns," accounting for exactly 31.8% of the total.
Although all cloud services emphasize the high level of security offered, they cannot completely eliminate concerns about risks such as information leaks because companies are entrusting their most important asset, their data, to outside service providers.
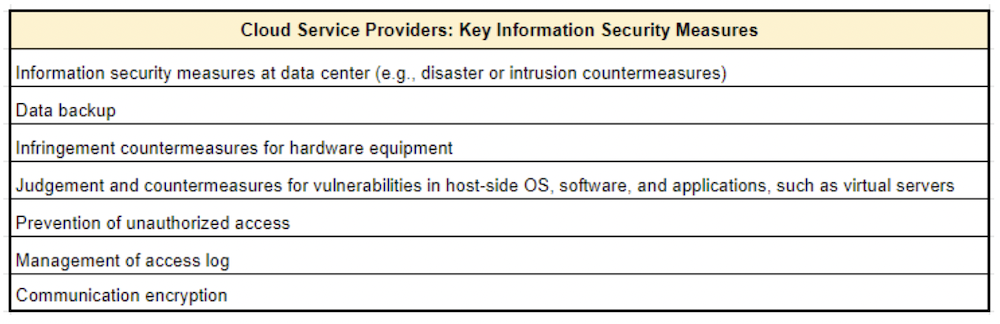
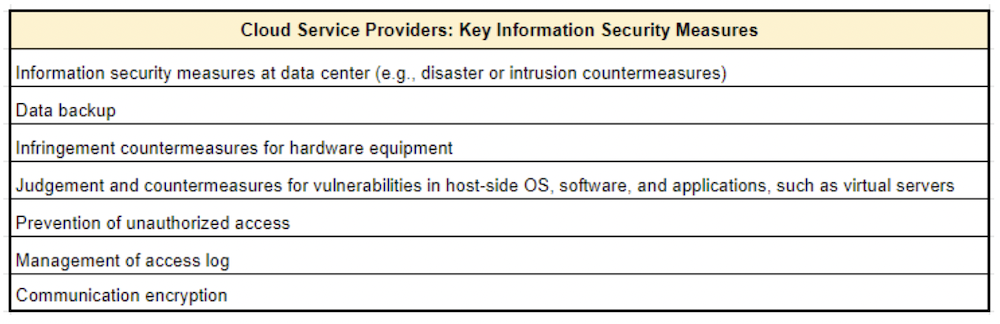
When considering cloud backup, it is pivotal that users review and confirm specific points referred to as the "Major Information Security Measures to be Taken by Cloud Service Providers" provided by the Ministry of Internal Affairs and Communications.
Speed and Data Transfer Volume
Since cloud backup involves storing data via the Internet, backup and restoration operations can take time depending on the data volume. In addition, since a large amount of data is transferred to a remote backup center, there are concerns about slow Internet connections, communication failures, etc. It may be necessary to set backup schedules outside of business hours, delete duplicate data, and other procedures to avoid complications for other areas of the business.
Stable Internet is Essential
Cloud backup requires that a copy of the data be securely stored on a remote, networked computing resource, so a stable Internet environment is essential. In comparison, a hard disk drive or external hard drive backup does not have that issue.
.png)
Why do we need cloud backup?
Despite these disadvantages, cloud backup is still integral to implement for two basic reasons: disaster preparedness and ransomware protection.
In a disaster-prone country like Japan, any company can suffer damage from a typhoon, earthquake, or other disaster and lose valuable data at any time and in any form. The servers used for cloud backup are generally located in data centers that are structurally designed to be earthquake- and fire-resistant and immune to power outages. That means that even if the office becomes unusable or inaccessible for some reason, data can be restored and business can continue as long as there is an Internet connection.
Even in the event of an attack, such as the encryption of critical data by ransomware, it is possible to protect the encrypted data by backing up the data to the cloud.
All of this makes cloud backup an effective means of crisis management.
.png)
What companies are suited for cloud backup?
Given the above requirements, cloud backup is particularly suited for companies whose data is essential to their business. DX (Digital Transformation) is currently being promoted in the Japanese business scene, and cloud backup is crucial for companies that are trying to create new value by making full use of digital technology.
What companies are not suitable for cloud backup?
For companies that already have an on-premise backup system in place and do not expect the amount of data to increase in the future, the benefits of cloud backup may not be significant. Nevertheless, even these companies should still consider this option when thinking about disaster management and the risk of cyber-attacks.
.png)
Cloud Backup Useful in a Variety of Situations
Tsukaeru Cloud Backup provided by Tsukaeru.net is more than just a backup service. It also combines functions for protecting and using data in a single package.
As image backups are used instead of file backups, even if data is lost, it can be restored at high speed and business can get back to normal immediately.
In addition, different devices in the company can be centrally managed from an administrator account. Settings can be changed remotely, saving both time and money.
Cloud Backup Essential Component of Company Stability and Reliability
Tsukaeru Cloud Backup uses the highest level of security, which is also used by the U.S. military. All file transfers are protected with AES-256, including server-side encryption. Active Protection, an AI-based technology that shields data from ransomware attacks, instantly detects and intercepts suspicious modifications to protect data.
Tsukaeru Cloud Backup is the most powerful solution to cope with disasters and cyber attacks, both of which are increasing in frequency and intensity in recent years. Priced from 1,628 JPY per month (including tax), customers can choose from a variety of plans according to usage and capacity.
Please apply for a free trial to see how our service can meet your needs.
Click here to learn more about Tsukaeru Cloud Backup.
.jpg)
Call toll-free: 0120-961-166
Office hours: 10:00-17:00
Cyber attacks are a growing threat that seems to have no bounds. On March 24, 2022, similar to February 23 and March 1, the government again issued an alert, "Strengthening Cyber Security Measures in Light of the Current Situation.”
For all companies, including small and medium-sized enterprises, there is a need to not only strengthen security measures to minimize the risk of infection, but also back up data for recovery in the event of infection.
Tsukaeru Cloud Backup, provided by Tsukaeru.net, is a service that combines not only backup functions but also provides data protection and usage in a single package and has become a popular choice for many companies.
Below, we will once again discuss the need for backups and examine the Tsukaeru Cloud Backup features.
Three steps to keep your company's data safe
With the incorporation of IT tools into all aspects of business and DX (digital transformation) changing how the world does business, the value of data to companies is increasing.
The following are three recommended data security steps a company can take to protect this important asset:
Save data in digital format
In addition to security enhancement, the Japanese government's promotion of "work style reform" and environmental protection are also encouraging companies to go paperless. However, the real-world implementation does not seem to be going as smoothly as expected.
According to a March 2020 BizClip survey of approximately 2,500 people in Japan, the reality of eliminating the use of paper documents in many companies has emerged. For example, 66.5% of all respondents indicated that paper is used for "contract and application documents," 57.9% for "invoices and estimates to suppliers and customers," and 54.8% for "internal meeting materials.”
The survey also revealed that 76.7% of "contracts and application documents," 64.2% of "invoices and estimates to suppliers and customers," and 56.6% of "internal meeting materials" were filed and stored in paper form without being scanned or converted to data.
When important corporate data is not digitized and only preserved in paper-based storage, it is exposed to the risk of loss, as well as disaster. To reduce these risks, company data and files should be digitized and stored securely.
.jpg)
Save data in multiple locations
Traditionally, the "3-2-1 rule" has been proposed for backups. This guideline was first presented in 2012 by US-CERT, which is operated by the U.S. Department of Homeland Security's Cybersecurity and Infrastructure Security Administration (CISA).
The term "3-2-1" means that, for critical data, there are three copies stored on at least two different types of recording media, and at least one copy is stored off-site.
Initially, this rule was considered to be too time-consuming to implement, but in recent years it has been reiterated and recommended by experts as a ransomware countermeasure. This 3-2-1 rule has become a cost-effective and feasible choice even for small- and medium-sized companies, especially with the increasing availability of cloud storage services that offer offsite options.
Use data backup tools
Backups can be implemented in a variety of ways. For example, Windows comes equipped with backup settings that allow you to periodically copy and store data on your computer to an external hard drive or another device on a regular basis.
However, since the amount of data held by many companies can be quite large, a dedicated backup tool is another option. For example, Tsukaeru CloudBackup by Tsukaeru.net not only provides backup functions but is also a service designed with data usage functions in mind, making it a highly effective and flexible solution.
Are backups really necessary?
As mentioned above, backups are the primary means for companies to protect their valuable data. However, even though many people know that it is important, they often put off creating backups for a variety of reasons. The following two issues clearly show the danger of not backing up your data.
.jpg)
Company data loss = major damage
It goes without saying that data loss can be a major blow to a company.
The loss of valuable data, such as customer information or research related to product development and marketing, can cause immeasurable economic damage to a company.
In addition, the cost of recovering from such a loss can be enormous. A hypothetical example in Japan would be the flooding of an office of a small business with 15 employees. It would be impossible to continue operations. If it took one month to restore the office, including the data, the employees might have to work overtime during that time, costing the company as much as three million yen. The company would also be forced to suspend operations for that month, resulting in a loss of sales of five million yen, for a total damage cost of eight million yen.
In fact, according to a research report from Texas State University, 94% of companies would go bankrupt within two years if all internal data were lost.
Data loss due to disaster or cyber attack
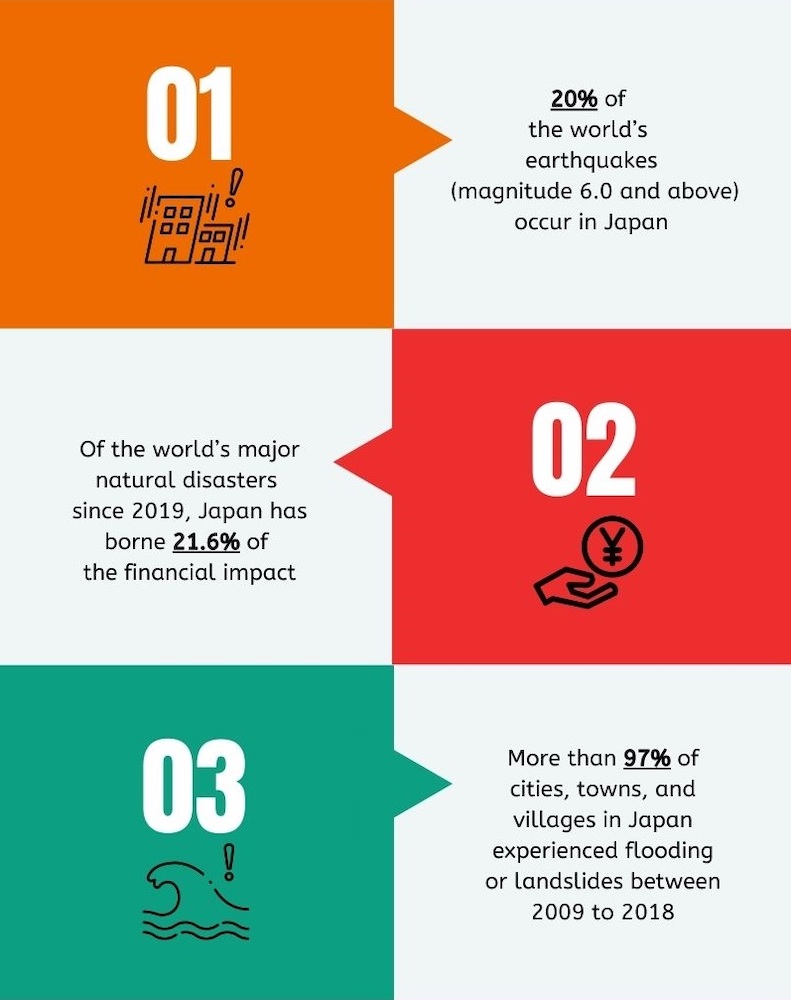
According to the Global Climate Risk Index (2020 edition) published by Germanwatch, Japan was ranked 62nd from 1999 to 2018, but in 2018, it was ranked first. With recent flooding and typhoon damage, as well as the Nankai Trough and Metropolitan Area earthquakes that are expected to occur in the future, a business continuity plan (BCP) is essential for any company in Japan.
In addition, according to a survey of more than 15,000 websites in Japan conducted by Cyber Security Cloud, Inc., access by cyber attackers has increased sharply since February 16, 2022, up to 25 times more than the average of the last three months.
Not just large companies, but also supply chains have been the target of attacks, and in March 2022, Toyota-affiliated Kojima Press Kogyo suffered a cyber attack that forced the company to temporarily shut down all of its domestic plants.
An especially dangerous threat is ransomware, which encrypts and disables infected computers or systems, the connected hard disks, and data within the same network. Companies must pay a large ransom to regain access to data or systems or be forced to suspend operations. The lost profits and recovery costs can be enormous.
.jpg)
Tsukaeru Cloud Backup and the functionality you're looking for!
As mentioned above, backup tools is one method for companies to protect their data. Below we examine the functionality of Tsukaeru Cloud Backup.
Main Features
Centralized management with backup, restore, security, and other functions
Tsukaeru Cloud Backup setup is extremely easy, and multiple backup targets can be managed at the same time from anywhere at any time. They can be flexibly configured, and files and folders can be restored and downloaded individually. If the entire system is backed up, the computer itself can be restored.
All of this is made possible by the "image backup" method, which backs up the entire system image, including all apps, files, user accounts, and even the operating system, all at once. This allows for the immediate resumption of normal operations in the event of data loss.
World-class encryption/cyber security features
The highest level of encryption, also used by the U.S. military, is performed before files are uploaded, and all file transfers are protected by AES-256. The server side is also securely encrypted with AES-256, and cyber security functions are also fully implemented to protect your company's valuable data.
Effective disaster recovery (DR) measures
Disaster recovery (DR) refers to the recovery of damaged systems in the event of a disaster. Needless to say, the most important aspect of DR measures is to minimize the downtime of corporate activities.
With Tsukaeru Cloud Backup, daily backups are uploaded to our domestic data center to be prepared for any contingency. In the event of a disaster, with the touch of a button, operations are switched to a standby environment to enable business continuity.
Summary
Tsukaeru Cloud Backup is the most powerful solution for dealing with the increasing risks of disasters and cyber attacks. In addition, it is very simple to use, requires no technical knowledge, and can be easily set up in five minutes.
The affordable price of 1,408 JPY per month (two-year contract), including 200 GB capacity, one desktop computer, and three mobile devices enables a low-cost introduction.
A free trial is also available, so please feel free to contact us below for more information.
Click here to learn more about Tsukaeru Cloud Backup.
.jpg)
Call toll-free: 0120-961-166
Office hours: 10:00-17:00
According to the results of a Ministry of Internal Affairs and Communications survey published in October 2020, the adoption rate of remote work among prefectures (47 organizations) and government-designated cities (20 organizations) increased to 95.5%. However, in municipalities (1,721 organizations), which account for the majority, the rate appears to be only 19.9%.
In addition, the Ministry of Internal Affairs and Communications indicates that the most common reason for not implementing remote work systems was that "consultation and counter services do not fit in with remote work" (82.7%), followed by "concerns regarding information security.”
While there is reluctance on the part of many local governments due to security concerns, it is a fact that not only companies but also governments are becoming targets of cyber attacks.
Increasing number of virus attacks targeting municipalities
In order to protect information from increasing cyber attacks, in 2015, the Ministry of Internal Affairs and Communications published the following “three-tier measures” regarding information security for local governments.
1. Disable data export settings and two-factor authentication
2. Access control
3. Robust countermeasures against external attacks
However, as cyber attacks are becoming more sophisticated, it is necessary for local governments to further strengthen their countermeasures.
Below are three examples of virus attacks targeting municipalities:
Japan Pension Service: Data leak due to unauthorized access
This 2015 incident, which triggered the above-mentioned “three-tier measures” by the Ministry of Internal Affairs and Communications, was unauthorized external access of the Japan Pensions Service system that resulted in the leak of approximately 1.25 million pieces of personal information. The cause is believed to have been a staff member who opened an infected file attached to an email.
Hiroshima Prefecture: 23 municipalities targeted for attack
Starting on February 16, 2022, the cloud service used by Hiroshima Prefecture and 23 municipalities in the prefecture was hit with a distributed denial-of-service (DDoS) attack over two days. This cyber attack technique disrupts the normal functioning of a website or server by sending an overwhelmingly large amount of Internet data. As a result, the websites of the affected organizations experienced poor connectivity. However, the demands and objectives of the attackers were not determined.
Aichi Prefecture: Attack on PCR testing system
On February 5, 2022, an Aichi Prefecture employee launched the prefecture’s PCR inspection system. Instead of the Japanese text that usually appeared, there was a message in English on the screen, and the employee discovered that the system was unusable. A subsequent investigation revealed that the server managing the system’s data had been attacked by ransomware. No personal information was leaked as a result of the attack, but the server was forced to shut down temporarily.
.jpg)
Security awareness when working outside the office
On February 23, 2022, the Ministry of Economy, Trade, and Industry (METI) issued a statement titled "Reminder to Strengthen Cyber Security Measures in Light of Recent Developments.” In the statement, METI listed security measures that companies and organizations should take, as well as expanding their awareness of cyber attack threats due to the increased potential risks. The following is an examination of some of these measures.
Important digital habits in the era of remote work
Confirm that simple passwords are not used
Obviously, passwords must be used when accessing Internet services; however, the same passwords should not be used repeatedly. Also, whenever possible, passwords should be at least 12 characters in length and should consist of a mixture of symbols, numbers, and upper and lower case alphabetic characters.
Use multi-factor authentication
Multi-factor authentication refers to an authentication system that combines two or more of the three authentication factors: “Something You Know,” Something You Have,” and “Something You Are.” Recently, passwords alone are no longer considered to be sufficient security, and multi-factor authentication is beginning to be adopted by many cloud services.
One example of multi-factor authentication in use is when withdrawing cash from an ATM: the combination of the physical card as “Something You Have” and the password as “Something You Know.” For websites, "one-factor authentication" using only passwords has been the mainstream for many years. However, in September 2018, Microsoft declared the "end of the password era," and since then, multi-factor authentication has been adopted by many cloud services. Currently, the most widely used multi-factor authentication method is logging in with an ID and password (Something You Know) and entering an authentication code generated by a smartphone app (Something You Have).
Use IoT devices securely and wisely
Today, the “Internet of Things” (IoT) is everywhere, in homes and workplaces, including home appliances, automobiles, office multifunction devices, factory sensors, and surveillance cameras. Of course, government agencies are no exception.
It is important to understand that as long as IoT devices are connected to the Internet, they present the same security risks as computers and smartphones. In fact, IoT devices are already the target of malware and other cyber attacks that affect data or functionality. As far as municipalities in Japan are concerned, there have been cases of unauthorized access to surveillance cameras in rivers and other areas in 2018.
Because these vulnerabilities in devices that control the connection to the Internet are often exploited in attacks, it is important to promptly install the latest firmware, updates, and other security patches.
.jpg)
Never open unverified attachments or URL links
Since its discovery in 2014, the Emotet malware continues to be a problem around the world and is reported to have resumed its attacks in November 2021, after a sharp decline in infections in Japan since April 2021. According to the Japanese Information-technology Promotion Agency (IPA), as of February 2022, the number of incidents is still increasing and continued caution is required.
The modus operandi of Emotet's attackers is simple and consistent. They trick victims into opening email attachments or clicking on URL links to infect their devices and steal email information. Not only that, if initially successful, the infection can spread throughout the system to infect other terminals, other companies, and other organizations.
Therefore, even if an email appears to be valid, perhaps from an important customer, business partner, or acquaintance, it is important to make a habit of carefully checking whether or not it is genuine before opening the attachment or URL link.
We also recommend "Tsukaeru Mail Buster" by Tsukaeru.net as another solution. This excellent service blocks junk and targeted attack emails before they reach the email server. As it is a completely cloud-based email security service, there is no need for installation on individual computers and no need to update to the latest version.
Backup data
One of the most common cyber attack threats that both government and private companies face is ransomware. According to the METI, the average ransom paid by companies affected by ransomware in Japan is approximately 114 million JPY (1.0 million USD).
One essential countermeasure is to store backup data in offline storage. In this way, in the unlikely event of a ransomware infection, the backup data can be restored after the storage is completely initialized and the ransomware is erased.
.jpg)
Tsukaeru Cloup Backup
In addition to prefectures and government-designated cities, remote work is expected to be embraced by local municipalities in the future. Not only will employee awareness of cyber attack threats need to be increased, but the on-site systems will also need to be modified appropriately.
One popular solution for this situation is Tsukaeru Cloud Backup provided by Tsukaeru.net. This cloud-based service combines not only backup functions, but also protects and allows data usage in one single and convenient package.
Easy to use & security brings peace of mind
Service stability is especially important for government agencies. In this regard, Tsukaeru Cloud Backup employs an "image backup" method that creates a copy of the entire system at once, allowing normal operations to quickly resume even in the event of data loss.
The service also uses the highest level of security, the same as the U.S. military, protecting all file transfers with AES-256 encryption. In addition, Active Protection, an AI-based technology, immediately detects and intercepts suspicious modifications to files, backup data, and backup software to protect valuable data from ransomware attacks.
The affordable price of 1,408 JPY per month (two-year contract), including 200 GB capacity, one computer, and three mobile devices enables low-cost introduction.
Please feel free to contact us below to find out about a free 30-day trial!
Click here to learn more about Tsukaeru Cloud Backup.
.jpg)
Call toll-free: 0120-961-166
Office hours: 10:00-17:00
The Japanese National Police Agency announced on January 28, 2022, that the number of arrests related to cyber crimes in 2021 was 12,275, an increase of 24.3% from the previous year and the highest number of arrests in any year. 2021 saw a series of cyber attacks that brought social infrastructure, such as medical institutions, to a standstill in Japan. The targets of these attacks were not just large corporations but also small- and medium-sized enterprises, small vendors, and suppliers.
As these threats are becoming more common in the modern business world, in today’s blog post, we will review cyber attacks and the best ways to deal with them.
What is a cyber attack?
A cyber attack is an attack that harms a targeted computer or system through the Internet or other networks. The main types of damage include data theft, leakage, destruction, and tampering. An effective cyber attack can wreak havoc on a company’s business.
Increasing number of cyber attacks: An overview
According to the “Recent Trends in Cyber Attacks” report released by the Japanese Ministry of Internal Affairs and Communications in June 2021, the number of unauthorized accesses or attacks in Japan reached 2,960 in 2019, almost double the 1,486 incidents that occurred in 2018. In addition, the number of attacks targeting remote work environments in 2020 increased by 340% compared to 2019, and the number of phishing attacks in 2019 increased by 280% in comparison to 2018.
For example, the Emotet malware, often referred to as the “scariest virus,” has been spreading globally since the summer of 2019. This cyber attack method impersonates a business partner by using actual text from a previous email exchange and sends an attachment with an embedded malicious program. The damage from Emotet is estimated to be as high as $2.5 billion worldwide.
Attack characteristics and common tactics
One of several characteristics of recent cyber attacks is the targeting of remote workers, whose numbers have increased in response to the COVID-19 pandemic. With more and more devices and computers being taken out of the office, attackers are focusing on endpoints with weak security.
As mentioned earlier, attacks are also directed at the supply chain, where security is also weaker. Once in the supply chain system, the attackers then try to break into the corporate network with the aim of accessing confidential information.
.jpg)
Common types of cyber attacks
In the following section, we will examine five common cyber attacks and their modus operandi.
Unauthorized access
As the name implies, unauthorized access is a type of cyber attack in which a password-protected system is illegally accessed to steal data. In many cases, the intrusion is made by analyzing or analogizing passwords. Therefore, proper password settings and regular password changes are effective preventative measures. According to data released by the Japanese Metropolitan Police Department, the Ministry of Internal Affairs and Communications, and the Ministry of Economy, Trade, and Industry (METI) in March 2021, the number of unauthorized accesses targeting general companies, as compared to other institutions such as government agencies and universities, has been increasing rapidly, especially since the beginning of Japan’s new Reiwa era in 2019, accounting for more than 95% of the total.
In addition, according to data released by the IPA (Information-technology Promotion Agency, Japan) in February 2021, of the 135 cases of unauthorized access received by the agency in the second half of 2020, 44 cases were caused by the above mentioned Emotet virus, and 21 cases were related to ransomware.
Rootkit attack
A rootkit attack is a technique in which several malicious programs are used in combination to target a computer to infect it with a virus. If successful, the malicious software works quietly behind the scenes and continues to send data to the attacker.
Many rootkit attacks are designed to operate in the deepest areas of the operating system (OS), making detection extremely difficult, not only for ordinary security software but also for special rootkit scanners. Even if detected, it can take a great deal of time to remove rootkits and will require a reinstallation of the OS.
SQL injection
Most web server databases are composed of a database language called SQL. However, if the server security is weak, it is possible to exploit the SQL command text with a technique known as SQL injection, which can result in information being altered or leaked.
In January 2022, Nichinoken, a major cram school, announced that its website web server had been illegally accessed, and up to 280,196 email addresses of people who had requested informational materials may have been leaked. It is thought that the cyber attack method was an SQL injection.
DDoS attack
A DDoS attack is a technique in which a large number of computers overwhelm and shut down a specific server by simultaneously sending access requests. The computers used in the attack are distributed across multiple networks, making it difficult to take effective countermeasures against the attack.
In recent years, an increasing number of DDoS attacks have targeted IoT devices with weak security. In addition, there are many small-scale and highly covert attacks that aim to reduce server performance for long periods of time without causing the server to shut down. This can cause enormous damage to companies with them being unaware of what is happening.
Cross-site scripting
Currently, most websites use a scripting language called JavaScript. Cross-site scripting (XSS) takes advantage of website vulnerabilities and embeds code that exploits JavaScript functions to alter the site.
.jpg)
How to deal with cyber attacks
Companies around the world face a variety of cyber attacks that can come from any direction. In order to be better prepared, the following two points are important to consider.
Need for security awareness and effective countermeasures
According to Accenture’s 2021 survey of more than 4,700 senior executives at large corporations in 18 countries, including Japan, 55% of all respondents said their companies were unable to implement effective cyber attack countermeasures, rapidly detect problems, respond to and recover from cyber attacks, and mitigate damage. This is in spite of the fact that 82% of respondents said their companies had increased their investment in cyber security over the past year and that the number of unauthorized accesses increased by 31% from the previous year.
In other words, there is not only a need to increase investment in security but also raise security awareness within the company and implement effective countermeasures. No matter how much money is spent on building a strong system, it will be meaningless if employees are not security conscious and do not follow the rules. In order to raise awareness, it is more effective for the person in charge to remind everyone on a daily basis than to hold a large training session once a year. It is recommended that regular updates with relevant information are shared to encourage and educate everyone who is involved.
Advantages of using the cloud
As mentioned above, cyber attacks have become increasingly sophisticated in recent years, and attackers are constantly targeting areas where security is weak. In addition, with the rapid increase of remote work and the use of digital devices outside the office, there is a limit to the amount of security that can be achieved within the company alone.
To cope with these changes in environment, cloud-based security measures are gaining attention. In the cloud, it is possible to prepare for the threat of cyber attacks in real-time and also to manage devices outside the company.
.jpg)
Tsukaeru Cloud Backup
Tsukaeru Cloud Backup from Tsukaeru.net uses Acronis Cyber Protection, used by more than 500,000 companies in 150 countries around the world, to protect your valuable data from unauthorized access, cyber attacks, and viruses.
Easy to use + Strong security
Tsukaeru Cloud Backup is the most powerful solution to protect your corporate data from cyber attacks, as well as disaster and hardware failures. In addition, it is very easy to use, requires no specialized knowledge or complicated installation, and can be set up in five minutes.
The low price of JPY 1,408 per month (two-year contract), including 200 GB capacity, one PC, and three mobile devices, makes the service an easy and affordable choice.
Please feel free to contact us below to find out about a free 30-day trial!
Click here to learn more about Tsukaeru Cloud Backup.
.jpg)
Call toll-free: 0120-961-166
Office hours: 10:00-17:00
Compared to the early days of computers, the need for backups has become self-evident, and most users, whether individuals or companies, are now backing up their data in some way. However, we need to consider whether our current backup methods are actually “safe.”
This is especially important as the digital society that surrounds businesses is constantly changing by the minute, and backups need to evolve at the same pace.
In this blog post, we will look at some of the reasons why and how every company should rethink their backup strategies.
Growing danger of data loss in a digital society
According to a March 2019 global survey by Acronis, 65% of consumers and 29% of businesses have experienced data loss leading to downtime. It is important to note that 93% of these consumers and 97% of these businesses backed up their data at least once a year.
The survey results indicate that just having a backup plan is not enough to avoid problems that could lead to downtime. The question is now not whether you have backups or not, but what is the best backup method that will bring peace of mind to your company.
Ever-increasing data volume & protection awareness
There are several reasons why the risk of data loss is increasing, even with backups. The first is that the amount of data held by companies is increasing drastically every year.
According to a March 2020 global study published by Dell Technologies, the average amount of data managed by companies jumped from 1.45 PB (Petabyte = 1,000 Terabytes) in 2016 to 9,70 PB in 2018. Furthermore, in 2019, it increased by 40% to 13.53 PB.
In addition, 81% of the companies surveyed responded that their current data protection solutions are not sufficient to meet all future data needs. They also reported that they feel that risks, such as cyber attacks, are increasing along with data volume. In fact, the average loss due to data loss also increased from USD 995,613 (about JPY 115 million) in 2018 to USD 1,013,075 (about JPY 117.6 million) in 2019. From the results, it is obvious that companies are struggling to cope with the ever-changing digital society.
.jpg)
How to keep your data safe
It is highly unlikely that anyone thinks “We have so much data, so a little loss isn’t a bad thing.” In our digital society, the importance of data to businesses cannot be overstated.
Below are three of the most common ways to keep your ever-growing data safe.
Local backup
Backing up your data to a device that you have at hand, such as a hard disk, a USB memory stick, or an external hard drive, a local backup is the simplest method and has the advantage of ensuring quick data retrieval.
Cloud backup
As the saying goes, “Don't put all your eggs in one basket.” Cloud backup stores your data in a separate location from your local environment. This protects your original files and local backups from being destroyed in a natural disaster or compromised by a cyber attack that engulfs the entire network. Another advantage of cloud backup is that users can access files and data from anywhere.
Malware: Security measures
When considering backup methods, it is crucial to understand how to protect your data from cyber attacks such as malware. This is especially important because ransomware, a type of malware that infects servers and systems, and then encrypts data, rendering it unusable, can easily spread to backup data as well.
What this means is that no matter how many backups you have made, if they are accessible from a computer or system that has been infected by ransomware, there is a high possibility that they will also be infected and encrypted, making recovery impossible. This is why, even if you choose cloud backup, you need a secure backup solution with ransomware protection.
.jpg)
Does your company use the cloud?
According to the 2021 White Paper on Information and Communication (Japanese Ministry of Internal Affairs and Communications), 87.1% of responding companies felt that cloud services were effective (“very effective” at 32.5%; “somewhat effective at 54.6%). In addition, 36.5% of companies answered that the service they used was “data backup,” an increase from 31.4% in 2019, indicating that the number of companies choosing cloud solutions to prepare for potential data loss is steadily increasing.
Benefits of using the cloud
Based on the above assumptions, the benefits of using the cloud can be summarized by the three following points:
1. Data is stored in a remote location, reducing the risk of loss.
2. Data can be accessed from anywhere via the Internet making it less location-based.
3. Backups are automatic and hassle-free.
Tsukaeru Cloud Backup
Tsukaeru Cloud Backup, provided by Tsukaeru.net, is a popular choice of many small- and medium-sized companies for their cloud backup needs because of its high-cost performance and ease of installation.
Using the cloud: Easy & Secure
Tsukaeru Cloud Backup is based on the image backup method. With regular file backups, it is necessary to install the OS on a new machine and reinstall the required applications before finally restoring the data and files. Image backups can significantly shorten the process, allowing immediate resumption of normal operations in the case of data loss. In addition, we have introduced “Active Protection,” an AI-based technology that protects data from ransomware and other cyber attacks by detecting risks before problems occur.
For the low price of JPY 1,408 per month (2-year contract), our service provides a 200 GB capacity for one PC and three mobile devices, making it an affordable and easy backup option for your company.
We are also excited to offer a free 30-day trial to discover how Tsukaeru Cloud Backup can help you keep your data safe and secure. Please feel free to contact us below to find out more.
Click here to learn more about Tsukaeru Cloud Backup.
.jpg)
Call toll-free: 0120-961-166
Office hours: 10:00-17:00
Hard disk drives (HDD) and solid-state drives (SSD) are common data storage devices and are growing in capacity and speed as the technology evolves. While these increases and lower prices benefit users, there is still one major risk: losing all your data at once if the HDD or SSD fails.
As data is always at risk from malfunctions, viruses, malware, and other disasters, backups are essential for data protection. In this article, we’ll take a deeper look at backups and their importance.
Backups are important, but…
Of course, we all know the importance of backups. However, it can be a real hassle to set up, and there are more pressing things to do. I’m sure you’ve found yourself thinking, “It’s fine. Nothing is going to happen. I’ll just do it later.”
30% of people have never backed up their data!?
According to one survey, about 30% of people in the U.S. said that they have never backed up their data before. Even though so much data is stored on computers and smartphones, the reality is that many people still have no experience or understanding of backing up their data.
The current state of backup in Japan
Now that smartphones have similar storage capacity as computers, protecting data, especially important information such as address books, photos, and videos, on mobile devices is becoming equally important. However, a survey conducted by TIME & SPACE in 2020 in Japan found that 40.4% of respondents indicated that they “Don’t keep backups.” In terms of explaining why, 29.2% chose “I don’t know how,” 27.0% chose “It’s too much trouble,” and 17.7% chose “I’ve never bothered.”
.jpg)
Why should you backup your data?
It can be surprising how many people in the U.S. and Japan do not back up their data. Especially in the case of smartphones, important and irreplaceable data can be lost, and there is a strong possibility that it can never be recovered.
Given the situations described below, the risk of data loss is ever increasing.
Japan: High risk of disaster
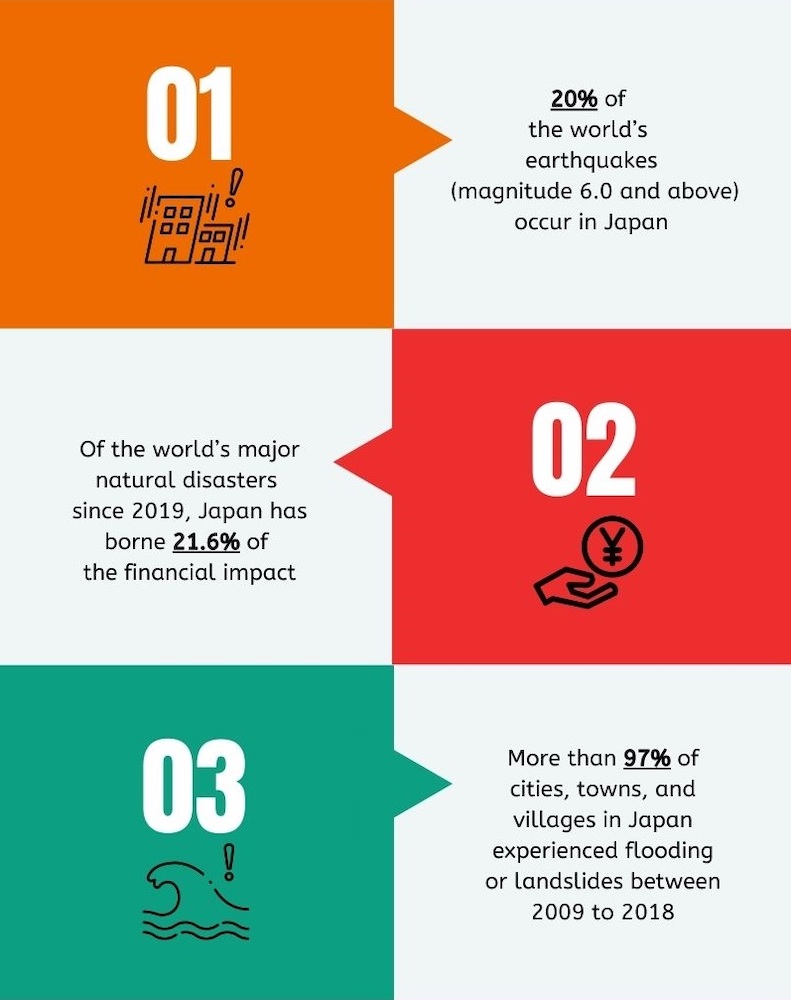
While Japan is blessed with an abundance of beauty and nature, it is also a country that is prone to natural disasters that can wreak havoc.
For example, with only 1% of the world’s landmass, Japan has 20% of the world’s earthquakes (magnitude 6.0 or higher).
In addition, recently the risk of flooding and landslides due to climate change and urbanization has also increased. The frequency of short-duration torrential rainfall with precipitation of 500 mm or more per hour has increased almost 1.4 times in the last 10 years as compared to the ten years between 1976-1986.
The Japan Meteorological Agency warns that if climate change continues at current rates, the number of days and frequency of heavy rainfall will be 20 times higher by the end of the century. Whether a company or an individual in Japan, it is essential to be prepared for the risk of data loss given these risks.
Cyber attacks and malware on the rise
On October 31, 2021, more than a dozen printers in a Tokushima Prefecture hospital, without warning, started printing at the same time. They produced an identical message, “We stole and encrypted your data. If you don’t pay the reason, we’ll disclose the data.” Due to the ransomware attack, the medical records of 85,000 patients were suddenly inaccessible.
The number of attacks like the one above is increasing. 33.8% of companies in Japan reported that the number of cyberattacks in April 2020 had increased as compared to the same month the year before, much higher than the 5.9% who reported that the number was lower. Cyber attacks are on the rise due to the spread and expansion of remote work, digital transformation (DX) in society as a whole, and the increased use of IoT devices.
.jpg)
The inevitable “life span” of a computer
On top of the risks of disasters and cyberattacks mentioned above, another possibility is HDD failure.
How long will a computer last?
As a computer’s lifespan depends on the main unit and the conditions of use, it is difficult to know how long it will last. However, five years is considered to be the life expectancy for a computer, while an internal HDD is four years. An external HDD is even shorter, about three years (about 10,000 hours). HDDs are designed to read and write data on the surface of a disk, which wears down over time. The lifespan of a disk may be even shorter in an environment with high humidity and room temperature.
SSDs, on the other hand, have no moving parts and on average last for about five years. In either case, the end of the lifespan for a computer or storage drive will eventually come.
Regular backups are the safest choice!
For peace of mind, the best option is to back up your files and data on a regular basis so you do not panic if something suddenly happens.
While there are a variety of ways to back up your files and data, such as an external HDD, the safest and most recommended way is to use cloud storage. With a cloud backup service, automatic backups save your important files and data to a secure, remote server. Compared to other methods, this is the easiest and more reliable method.
Tsukaeru Cloud Backup
Provided by Tsukaeru.net, Tsukaeru Cloud Backup is a popular cloud backup choice of many small- and medium-sized businesses due to its high-cost performance and ease of implementation compared to competitors.
Various backup options for files, data, and even entire OS
Tsukaeru Cloud Backup is the most powerful solution for data protection from natural disasters and cyberattacks.
For backups, we offer fast and reliable restores for problems with applications, systems, and data on any device.
In addition, your data is protected with complete security measures that detect risks before they occur.
The 1,408 JPY per month (two-year contract), including a 200GB capacity for one computer and up to three mobile devices, offers an easy way to implement a cloud storage system at a low cost.
A free trial is also available to experience Tsukaeru.net’s Tsukaeru Cloud Backup service.
Click here to learn more about Tsukaeru Cloud Backup.
.jpg)
Call toll-free: 0120-961-166
Office hours: 10:00-17:00
With ever expanding digital transformation (DX), a company’s data also increases in volume and value. As a result, data protection is one of the top priorities for any company. This is especially true for companies located in Japan who need to prepare for two dangers that threaten their data security: natural disasters and cyber attacks. In this article, we will discuss the urgency of these threats and the preventative measures that should be implemented.
Japan: One of the most disaster prone countries in the world
While it goes without saying that Japan is a disaster-prone country, there are still many people who think that they and their companies are safe from the risks. However, based on historical records and research, the government and many scientific organizations are well aware of the risks and do their best to educate people about them. Business people operating in Japan would be well advised to pay attention to the following facts.
A history and future of disasters
・The probability of a Southern Ocean Trough earthquake is 70-80% over the next 30 years.
・The probability of a severe tremor (6 or higher on the Japanese “Shindo” scale) within 30 years in metropolitan Tokyo is 47%, 38% in Yokohama, 46% in Nagoya, and 30% in Osaka.
・Although the probability of future earthquakes in Tohoku and the Sea of Japan is relatively low, they have occurred in the and caused significant damage (e.g., the Niigata Chuetsu Earthquake and the Tohoku Earthquake in 2011).
・Flood damage in Japan in 2019 totaled 2.18 trillion JPY, the largest recorded amount of non-tsunami flood damage in a single year
・In August 2021, the Japan Meteorological Agency (JMA) issued a “Special heavy rainfall warning” and “General information on significant heavy rainfall due to the occurrence of linear precipitation zones in various areas. In Northern Kyushu, some areas reached 50% of their annual rainfall in less than a week in that same month.

Cyber attacks: “Disasters” in the digital world
In addition to real world disasters, there is another risk that companies should be wary of: cyber attacks. These digital disasters threaten more than just corporate data. The ransomware attack on the Colonial Pipeline fuel company earlier this year and the damage it caused to human lives and social infrastructure is still fresh in our minds.
Ransomware damage
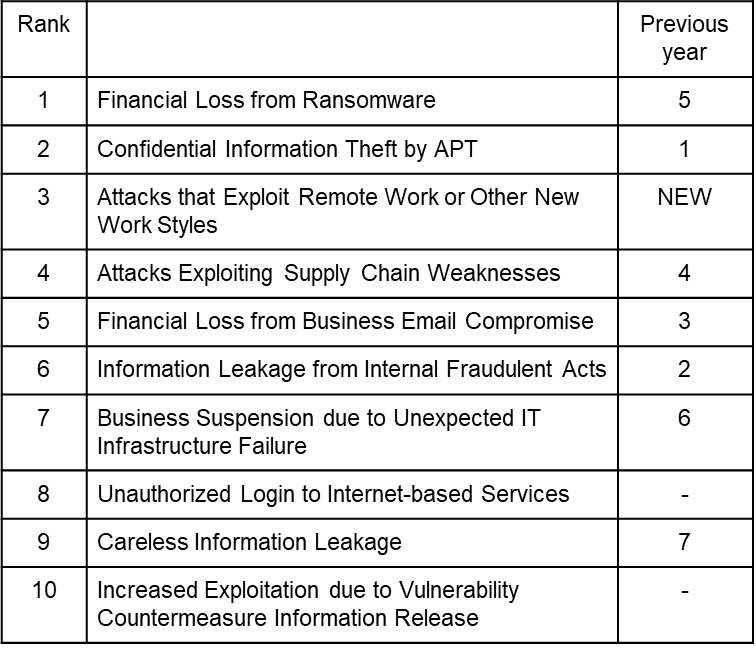
According to the August 2021 “10 Major Security Threats 2021” report from the IPA (Information-technology Promotion Agency, Japan), “damage from ransomware” is considered to be the largest threat for organizations.
Source:”10 Major Security Threats 2021” / IPA(Information-technology Promotion Agency)
https://www.ipa.go.jp/security/vuln/10threats2021.html
Ransomware is a virus-based cyber attack that encrypts the data stored on a company’s computer or server. or renders the device itself unusable. It is an extremely malicious cyber attack in which money or encrypted assets are demanded in exchange for data recovery or for not exposing confidential information.
In fact, according to data released by the Tokyo Metropolitan Police Department in September, ransomware attacks in the first half of 2021 increased by nearly three times compared to the second half of 2020. Of the affected companies, nearly 40% incurred a total of more than 10 million JPY in investigation and recovery costs.

Ransomware damage and attack routes in Japan
According to the Metropolitan Police Department report mentioned above, the routes of ransomware infection are through VPN devices (55%), remote desktops (23%), suspicious emails with attachments (13%), and others (10%). As companies have responded to the COVID-19 pandemic by implementing remote work and relying on remote desktops and VPN devices to allow outside connection to company networks, hackers are increasingly taking advantage of the disruption.
Keeping your data safe
The above information is a sobering reminder of the threats that corporate data faces in 2021.
However, companies should not let the fear of future possible threats derail their plans. Instead, they should take proactive and preventative action now.
Disaster countermeasures
One excellent way to prepare for natural disasters is to store company data in the cloud. By storing the data in a location that is both unlikely to be affected by a disaster and that is protected even in the event of a disaster, companies can easily restore their data to existing or new computers and devices. In addition, it is possible to retrieve only the necessary files and folders from the cloud back-up data to get up and running again.
Ransomware countermeasure
As a general rule, the best defense against cyber attacks should be mult-ilayered. As security threats are diverse and ever changing, it is possible to be better prepared for all kinds of risks by implementing overlapping defenses. Specifically, firewalls and WAFs should be installed to prevent intrusion from the outside and internal security systems should be created.
To be better prepared against ransomware, one of the most alarming cyber attacks, please follow the three following steps.
■Prevent intrustion
・Always update security software, operating systems, and major software
・Do not click on suspicious links or pop-ups, and do not open suspicious emails
・Use trusted websites
■Prevent attacks
・Use the latest security products and procedures
・Do not involve those with administrator authority in daily operations if possible
■Recovery
・Regularly backup data and systems
・Maintain at least one offline data backup

Tsukaeru Cloud Backup
Finally, an effective solution to protect your data from two ever present threats to your company and your data: natural disasters and cyber attacks.
Cloud Backup protects your data with the best security measures
Tsukaeru Cloud Backup is the most powerful solution that combines backups as a natural disaster countermeasure and security as a cyber attack countermeasure.
Backup protocols provide quick and reliable restoration for all incidents that affect applications, systems, and data on any device.
Security protocols detect threats before they occur and protect data with full security measures.
For a low cost of 1,408 JPY per month (two-year contract), Tsukaeru Cloud Backup provides a 200GB capacity service for one personal computer and up to three mobile devices.
To find out about our exciting free trial offer, please contact us using the link below.
Click here for more information on Tsukaeru Cloud Backup.
.jpg)
Call toll-free: 0120-961-166
Office hours: 10:00-17:00
The idea of "vulnerability" in regards to the Internet has been making an appearance on TV and in the media with increasing frequency. You may have seen headlines such as "ABC company's customer information was leaked" or "1,000,000 customer’s credit card information compromised in a cyber attack."
For Internet-based services, this is always a risk. The reality is that this is no longer only a problem for large corporations. Now small- and medium-sized enterprises (SME) have become targets of cyber attacks targeting known and new vulnerabilities.
In this article, let’s look at the basics of vulnerabilities that corporate webmasters and those who handle Internet services for business should know.
What is a vulnerability, anyway?
A vulnerability in this context is a security flaw in a software program or a computer network/system. Your first reaction may be, "Well, why don't they just create better security by making software without flaws?" Unfortunately, this is practically impossible. The amount of computer code that makes up software is enormous, and since that code is written by human hands, it is extremely difficult to create perfect software with no flaws at all.
Vulnerability exploitation: The fallout
A cyber-attack that successfully targets an unaddressed vulnerability can lead to serious damage such as a leak of personal information or website tampering. However, the results can be even more damaging and harder to repair. A security compromise can easily create a lack of trust from your customers and a long lasting, negative reputation, a death blow to many businesses.
As mentioned above, cyber-attacks are also becoming a growing problem for SMEs. One reason is that SMEs usually have smaller staff than large corporations with well-developed information system management departments and are less likely to have much time and money to spend on security measures and communication with providers, all resulting in greater vulnerabilities.
.png)
Cyber attacks: Types and examples
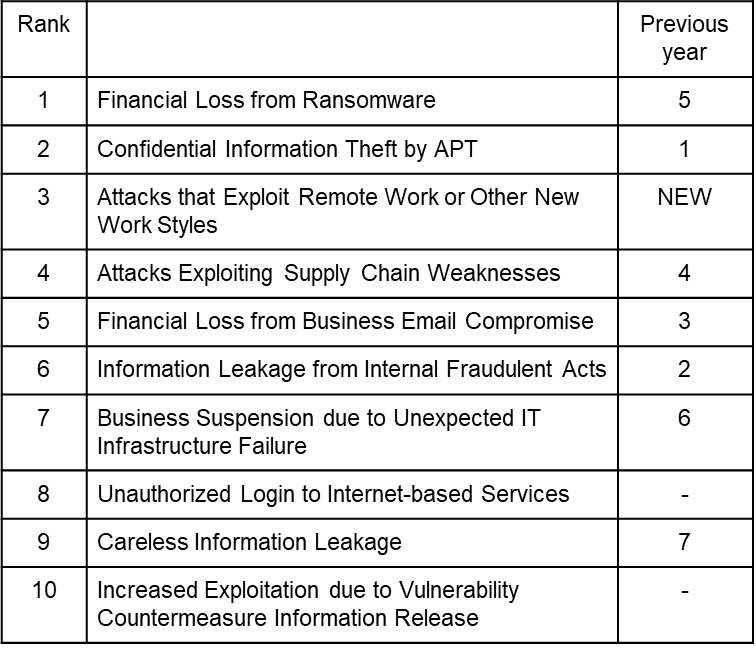
According to a report by the Security Center of the Information-technology Promotion Agency, Japan, cyber-attacks are included among the 10 major information security threats for organizations in 2021, for example, "Ransomware damage (No. 1)," "Confidential information theft from targeted attacks (No. 2)," "Attacks targeting new work styles, such as telework (No. 3)," and "Increasing exploitation of countermeasure information vulnerability after release (No. 10).”
Perhaps of greatest concern is the increase in cyber attacks targeting remote work employees. While remote-work security issues have been discussed previously, the percentage of remote workers has rapidly increased, as well as vulnerability exploitations. For example, in July 2020, a vulnerability was discovered in the web conferencing service ZOOM that allowed access to private meetings. Furthermore, in August 2020, a VPN product vulnerability was exploited to steal approximately 900 credentials and publish them on the Internet.
Preventative measures against cyber attacks
In order to minimize the possibility of cyber attacks that exploit vulnerabilities, we recommend that you enforce the following three ironclad rules of security on a daily basis.
.png)
Educate yourself
First of all, the most important thing is to have the best and most current information about security and vulnerabilities. If you are in charge of IT at your company, it may be a good idea to get advice from an expert or regularly read up on changes in the industry, new developments, and what the bad guys are doing.
Perform system updates
Always keep your operating systems (OS) and software updated, which contain not only enhancements but also fixes for vulnerabilities and bugs. Continuing to use an older OS is a significant security risk. However, in recent years, there has been an increase in the number of “zero-day” attacks, in which a vulnerability is discovered and exploited before the fix is distributed. This is just one reason why It is important to keep up with the latest security information to mitigate risks as much as possible.
Use a service with strong vulnerability countermeasures
While system updates and keeping up with the latest information are essential, you can also use services that are strong in protecting against vulnerabilities. For example, one such service is a Web Application Firewall (WAF), a network security system that protects customer and credit card information from cyber attacks targeting web application vulnerabilities.
It is also important to introduce a reliable cloud tool with basic security features such as backup and malware protection for remote work.
.jpg)
Tsukaeru Cloud Backup + Vulnerability Protection
Tsukaeru Cloud Backup+ (Plus) from Tsukaeru.net not only provides cloud backup functionality but also provides complete vulnerability countermeasures.
Virus detection with data scan
Tsukaeru Cloud Backup+ automatically scans for viruses and protects against malware lurking in your backups. If an infected file is found, it will be prevented from being restored from the backup, minimizing any damage.
Automatic vulnerability assessments
No matter how hard you try to keep up to date with the latest information and developments on vulnerabilities, there is a limit to how much you can do by yourself. Tsukaeru Cloud Backup+ automatically conducts daily vulnerability assessments, detecting problems that you cannot see before they occur and displaying the severity in using a color-coded system.
Tsukaeru Cloud Backup+ is an affordable service that provides both security management and cloud backup at the same time, with uncompromising security measures and ease of use.
To experience it for yourself, contact us to learn about our free, 14-day trial!
Click here for more information on Tsukaeru Cloud Backup.
.jpg)
Call toll-free: 0120-961-166
Office hours: 10:00-17:00
In our current digital age, most of our data is now stored on computers, allowing us to easily access our files from basically anywhere at any time. It also frees us from the need to print and carry paper versions of the information. Gone is the worry about losing or forgetting important documents on the way to that important meeting.
However, just because the materials have been digitized does not mean they are 100% safe! Just as there are specific problems with paper documents, digital files have problems that are unique to that medium. One of those problems is data failure, and when it occurs, you can lose access to valuable information, or even worse, your data can be completely lost.
So what exactly is data failure and how can you prevent it from happening?
Data failure classifications and causes
Data failures can be categorized into two main types: physical failures and logical failures, each with a different cause.
Physical failure
Physical failure occurs when the parts of the hard disk are physically damaged and will not boot properly. This may happen if a hard disk is dropped or damaged by a natural disaster (ie., flooding). It can also occur if the physical parts wear out and fail during normal use.
When a physical failure occurs, you may hear the hard disk make strange noises, such as a "ticking" or "knocking" sound. It may also ask to be formatted during operation, freeze up, or reboot frequently.
A strange noise could indicate that you have a "magnetic head failure," sometimes called a “head crash.” This is the part of the hard disk that reads and writes to the data recording surface called a platter, and if this condition continues, the platter will be scratched, causing severe physical damage, which may make data recovery impossible.
Another possible physical failure is "firmware failure." For example, an electrical event may cause damage to the hard drive’s logic board, causing problems with firmware, the software that controls the device. This could result in data reading and writing being impaired. However, a firmware failure may be difficult to distinguish from the logical failure described below.
Logical failure
A logical failure is a situation where the hard disk itself is not physically damaged, but the data and folder structure stored inside is faulty. Signs that a logical failure has occurred can be files and folders that cannot be opened, file names that are rewritten without permission, or the appearance of a blue screen.
One of the causes of logical failure is mishandling or human error which causes data to be accidentally or maliciously erased, initialized, or formatted. Another cause is "file system failure," where the file system, which can be described as a file organizer, is damaged when the user forcibly terminates the system while in the act of writing data. The data itself may not be damaged, but it may suddenly become inaccessible.
.jpg)
What to do in the event of data failure
Although some of the symptoms of data failure are described above, without expert knowledge, it is not easy to determine whether it is a physical or logical failure. The more important thing is to identify the cause and take appropriate measures to prevent the symptoms from worsening and making data recovery impossible. To that end, it is highly recommended to follow these three following suggestions.
(1)Do not keep the power on
When a hard disk is experiencing a physical failure, the magnetic head will also continue to move while energized, further damaging the platter. Turning the power off immediately could stop your data from being completely destroyed.
(2)Do not keep turning the power on and off
Repeatedly switching the power on and off to check the operating status or reset the device may lead to further scratches on the platters or data loss as in (1) above.
(3)Do not disassemble
While you may want to disassemble the hard disk in an attempt to determine the cause, the inner mechanism is very delicate and any dust and dirt that may get in could worsen the failure. Also, disassembling the hard disk by yourself may void the warranty and any recourse from the manufacturer.
How can you reduce the chance of data failure?
Preventing physical failure
Due to the nature of physical failures, unfortunately, there are only a limited number of prevention measures that can be implemented. Hard disks are basically considered to be a consumable item with a limited life span. If used for a long time, it is inevitable that some kind of problem will occur. However, it is possible to reduce the chance of occurance to some extent by careful handling of the device or computer and replacing the technology every few years. In the industry, the lifespan of a hard disk is generally said to be three to five years, and it goes without saying that regular backups are necessary considering the impossibility of predicting when a physical failure will occur.
Preventing logical failure
On the other hand, there are several effective measures that can be taken to prevent logical failures, such as access rights management and virus infection prevention.
.jpg)
Access Rights Management
As mentioned above, human error or mishandling is a surprisingly common cause of logical failures. The risk can be significantly reduced by setting and managing the access permissions for each system’s functions and data. It is vital to always determine who actually needs a function or file and reconfirm/review the access permissions.
Virus infection protection
Anti-virus is not only about preventing logical failures; it is the foundation of information security. It is important to be able to update software and check for viruses on a regular basis with no hassle. Taking care of your security is directly related to protecting your important data.
Regular cloud backups provide assurance and peace of mind
While working to prevent data failures, it is equally important to take measures to minimize potential damage to your business in case of a data failure. The safest and easiest way to do this is to have backups, especially ones that use cloud services. With a cloud backup of all your files, you can minimize the fallout of a data failure by restoring from your backups.
Full management functions and ransomware protection with Tsukaeru Cloud Backup
With your computer and data backed up to the cloud on a regular basis, you never have to panic if a data failure suddenly occurs. Even if it is caused by a virus, malware, or a ransomware attack, your backup files are not affected at all, allowing you to keep your business up and running.
To learn more about the popular Tsukaeru Cloud Backup service from Tsukaeru.net and how it can help you safely and easily protect your data, please visit our website.
Click here for more information on Tsukaeru Cloud Backup.
.jpg)
Call toll-free: 0120-961-166
Office hours: 10:00-17:00
It is difficult to overstate the importance of backing up your computer or smartphone. All your data, your files, your contacts, your photos, etc. are a vital part of your digital life. This is especially true in the business world where this accumulated data is a valuable asset, making backups a must.
However, when it comes to backups, there are those who say, "It takes too long for the backup to finish, and it's a pain…" Indeed, if you have a massive number of files on your computer, it can take a considerable amount of time, sometimes as much as half a day.
In this article, we will take a look at using the cloud to backup your data and ways to make that process easier and faster.
Cloud backup in Japan
According to a survey conducted by the Japanese Ministry of Internal Affairs and Communications (MIC) in 2020, the percentage of companies using cloud services has been increasing year by year. That year it reached 68.7% breaking down to 39.4% for "company-wide use" and 29.3% for "use in some offices or departments." Data backup accounted for 36.5% of cloud service usage, a further increase from 31.4% in 2019.
Cloud backup advantages
One of the biggest advantages of cloud backup is the lower installation costs compared to large, in-house storage devices. This is especially true for small or medium-sized businesses that do not have large budgets. In addition to the cost, cloud backup does not require an in-house professional staff to perform daily maintenance.
Even if a great deal of money and manpower is used to set up your own backup, this does not necessarily guarantee efficiency and reliability. Technology is constantly changing, and it can be a struggle to stay up to date and secure from new threats. With cloud backup, on the other hand, you can rely on a professional company to monitor and maintain the latest backup infrastructure for you, thus ensuring high reliability and efficiency.
In addition, cloud backup is easily scalable. One major appeal is that you can choose the data capacity according to the scale of your business and then increase it as needed.
Cloud backup disadvantages
One disadvantage of cloud backup is that everything happens through the Internet, which can result in bandwidth problems during busy times. One solution is to set the backup schedule outside of business hours. For example, with Tsukaeru Cloud Backup provided by Tsukaeru.net, you can set the bandwidth to better manage speeds. However, no matter when you schedule the backup, as long as it is dependent on an Internet connection and depending on the amount of data, it may take some time to backup and restore.
Different backup types and how to increase data transfer speeds
What can you do if your backups are slow and time-consuming? Here are some tips to improve backup speeds that you can implement immediately.
External HDD backup
One of the most common backup methods is to save everything to an external hard drive (HDD). In this case, there are two main ways to improve the speed.
The first option is to use a USB 3.0 compatible cable for the data transfer. USB 3.0 is a new USB standard that improves transfer speeds up to three times more than the conventional USB 2.0. However, this method requires that the computer, cable, and external HDD are all USB 3.0. compatible.
The second option is to use specialized file transfer software (not the default function of the operating system) that can increase speeds and reduce backup times even for older computers that do not support USB 3.0.
.jpg)
Things to consider when choosing a cloud backup service
Due to the current global situation, more and more companies are turning to cloud backup. However, backup speeds depend largely on the cloud service used, making it very important to choose the right service. In order to choose a service with the best backup speeds based on your needs, we recommend that you compare the following points:
Cloud backup method
There are three main methods to protect your data using the cloud: full backup, differential backup, and incremental backup. Each of them will be explained in the next section below.
Server Location
Uploading time can vary depending on how far or close the server is to you and your data. Even though your information is digital, it still has to be transferred to a data center that physically exists. Therefore, backups with a cloud service using Japan-based servers will be faster for clients in the same country as compared to services with overseas servers.
Data recovery restrictions
Even if your cloud backup is fast, it is of little use if it requires a long time to restore your data. Some services enforce a certain limit on the download capacity or speed when restoring data, so make sure to fully understand any limitations when considering your options.
Cloud backup types (full, incremental, differential)
There are several cloud backup types to choose from, and with Tsukaeru Cloud Backup, you can select the most suitable format according to your needs.
With our default settings, the initial backup is a full backup with the second and subsequent backups being incremental backups. However, you can change the settings to "Always full," "Always incremental," or "Always differential."
Full backup
.jpg)
Just as it sounds, this is a complete backup of all the files on your computer. The first time you create a backup with Tsukaeru Cloud Backup, it will be a "full backup" and therefore will take the longest time.
Incremental backup
.jpg)
By default, Tsukaeru.net creates an incremental backup for the second and subsequent backups. This method detects and backs up only those files that have changed or have been newly created since the last backup, whether it was a full or incremental backup. This significantly reduces the backup time compared to a full backup.
Differential backup
.jpg)
While similar to an incremental backup, a differential backup copies all of the files, new and old, that had been added or changed since the last full backup. Because of the larger amount of data, a differential backup can take longer compared to an incremental backup.
With Tsukaeru Cloud Backup, you can also set the second and subsequent backups to be differential backups.
Tsukaeru Cloud Backup: Stress-free data protection
Backing up your data often requires time and effort, and it can quickly become an annoying chore. However, it is extremely important to protect your data on a daily basis. To ensure that this happens, it is recommended that you choose a backup method and service that is as stress-free as possible. With Tsukaeru Cloud Backup provided by Tsukaeru.net, you can easily back up your data to a dedicated server in Japan in as little as five minutes. Of course, this service provides incremental backups, which are superior in terms of speed. There are also no speed or capacity limitations when restoring. Please visit our website at the link below if you are interested in learning more about Tsukaeru Cloud Backup.
Click here for more information on Tsukaeru Cloud Backup.
(1).jpg)
Call toll-free: 0120-961-166
Office hours: 10:00-17:00


.png)
.png)
.png)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)


.jpg)
.png)
.png)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
.jpg)
(1).jpg)
